Check Point: DNS Cache Poisoning Attack | Internet Security, Check Point: Through the Years
00:01:45
Обнаружено блокирование рекламы на сайте
Для существования нашего сайта необходим показ рекламы. Просим отнестись с пониманием и добавить сайт в список исключений вашей программы для блокировки рекламы (AdBlock и другие).
Check Point Software Technologies, Ltd. 360 роликов
87220 просмотров на сайте 12n.ru
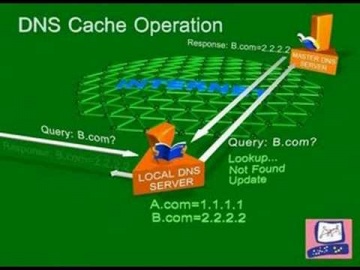
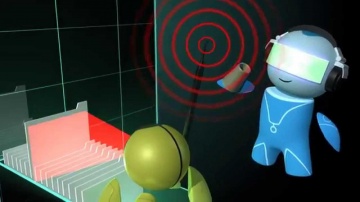
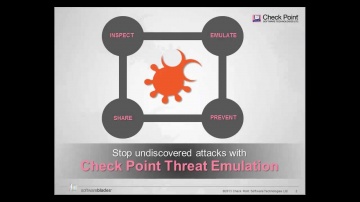
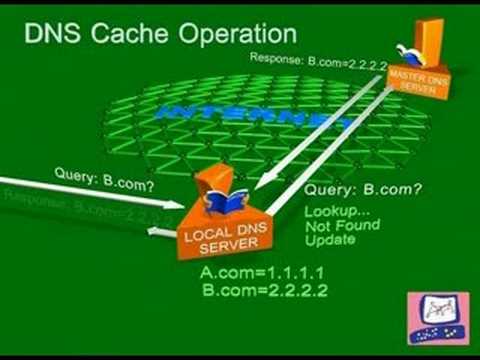
DNS Cache Poisoning Attack | Internet Security.
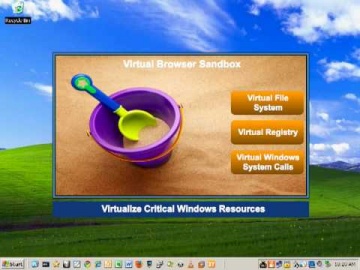
Software explains common DNS attacks. Learn More: DNS is the glue that holds the Internet, including web and e-mail together. A successful attack may severely impact the availability of an organization’s public facing web sites and e-mail. solutions help prevent and reverse these attacks.
развернуть свернуть