Поиск по тегу «hack» в разделе Видеокаталог
HD 01:01:35
Check Point: EU GDPR Webinar Replay
The European Union’s General Data Protection Regulation (‘GDPR’) poses the biggest change to the regulatory landscape of data privacy. To learn more visit: GDPR places significant policy and technical responsibilities on ANY organization ...
Cмотреть видео
Cмотреть видео
HD 00:30:26
Check Point: Who's Responsible for your Cloud Security?
A full breakdown of what is shared responsibility and the layers of security needed to protect you from security breaches in the cloud. For more information:
Cмотреть видео
Cмотреть видео
HD 00:29:43
Check Point: The Mobile Threat Landscape
From Judy to Blueborne, the proliferation of mobile threats has grown rapidly in the past year. In this session, we review the various types of mobile threats, how they spread and the damage they cause. We will also be providing practical ...
Cмотреть видео
Cмотреть видео
HD 00:06:53
Check Point: Top Cloud Cyber Security Challenges in 2018
Head of Product Marketing, Data Center and Cloud, Don Mayer, discusses some of the top cyber security challenges organizations face with the cloud in 2018. He dives into the amount of cyber attacks or cyber threats targeting the cloud and e...
Cмотреть видео
Cмотреть видео
HD 00:02:44
Check Point: CloudGuard SaaS Demo Series: Protecting Sensitive Data
For more information: Watch this short demonstration video to learn how CloudGuard SaaS, an industry-first software-as-a-service (SaaS) security solution, provides advanced security and sensitive data protection for SaaS applications such ...
Cмотреть видео
Cмотреть видео
HD 00:05:12
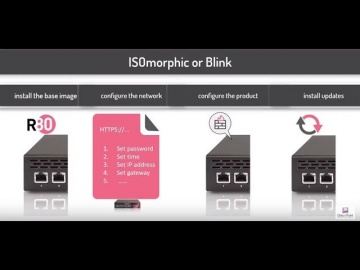
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:50:38
Check Point: Advanced Cyber Security for 2018 | Introducing 3 New products: Step into Gen-V of Cyber
For more information: is happy to welcome the 5th Generation of Cyber Security with 3 exciting new offerings: Infinity Total Protection (ITP), CloudGuard, and Smart-1 Security Management Appliances. • Infinity Total Protection is a gam...
Cмотреть видео
Cмотреть видео
HD 00:02:49
Check Point: Advanced Cyber Security for 2018 | Prevent Gen V Cyber Attacks with Infinity
More information: ... Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the fut...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
HD 00:17:04
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
HD 00:00:54
Check Point: Research Finds AliExpress Vulnerability: How It Works
To Read The Full Story Visit: Researchers at discovered that criminals have a new way to trick online shoppers via the massively popular AliExpress shopping portal using Java Script. After discovering the vulnerability, they immediate...
Cмотреть видео
Cмотреть видео
HD 00:06:01
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
HD 00:08:53
Check Point: CyberTalk: Conversations on the Cloud with ESG's Jon Oltsik | Cloud Security | CyberTal
To learn more about cybersecurity trends and challenges, check out An informal conversation between ESG principal analyst Jon Oltsik and 's Don Meyer, focused on cloud security: what to watch out for, how to secure against data breaches, ...
Cмотреть видео
Cмотреть видео
HD 00:04:00
Check Point: SandBlast Mobile: Quick Start Guide | Tech Bytes
This video is meant to show how easily you can get started protecting your Enterprise's Android and iOS Devices with SandBlast Mobile. More information: Topics covered: Ch1 - Activating Your Admin Account Ch2 - Logging into Your SandBlast...
Cмотреть видео
Cмотреть видео
HD 00:17:56
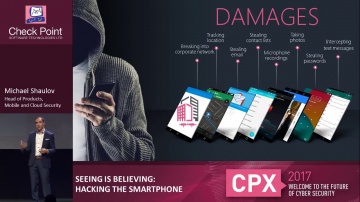
Check Point: Hacking the Smartphone | Mobile Cyber Hack Demonstration
Live demonstration of a smartphone hack, from Experience 2017. For more information visit: Watch Michael Shaulov, Head of Mobility Products at Software hack a smart phone in real time. Today every business is a mobile business, with req...
Cмотреть видео
Cмотреть видео
HD 00:01:55
Check Point: Optimizes Security with Gigamon’s Full Network Visibility
and Gigamon’s joint solution provides comprehensive network visibility, optimal performance and advanced threat prevention capabilities. For more information:
Cмотреть видео
Cмотреть видео
HD 00:07:58
Check Point: 2017 Cyber Security Survey
Donald Meyer, Head of Marketing, Data Center and Cloud, discusses top security concerns that IT professionals have regarding Cloud and Mobility security. For more information:
Cмотреть видео
Cмотреть видео
HD 00:07:15
Check Point: vSEC, The Future of Cloud Security
In this video, you’ll hear from Donald Meyer, Head of Marketing, Data Center and Cloud, where he discusses issues surrounding Cloud security and how organizations can better protect themselves from vulnerabilities in the Cloud. For more in...
Cмотреть видео
Cмотреть видео
HD 00:04:49
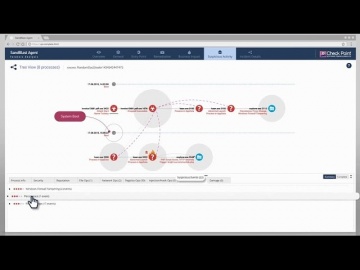
Check Point: SandBlast Agent Forensics
This video shows SandBlast Agent’s automated forensics analysis in action. For more information: It demonstrates SandBlast Agent’s power to instantly provide security teams with a crystal-clear understanding of cyber attacks, empowering t...
Cмотреть видео
Cмотреть видео
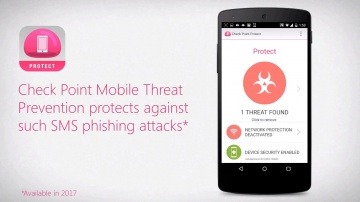
HD 00:02:12
Check Point: Anatomy of a Smishing Attack: Czech Posta App
A new smishing attack targeted users in the Czech Republic was discovered January 26, 2017. Smishing, or SMS phishing, is a vector attackers use to send SMS messages from supposedly legitimate organizations. These messages persuade users t...
Cмотреть видео
Cмотреть видео
HD 00:02:37
Check Point: Protecting Mobile Devices Together - ElevenPaths – Telefonica and | Mobile Security
“Mobile devices are critical to the way we do business today. With cyberattacks growing in sophistication and frequency, exposing both the business and personal data we store on smartphones and tablets, mobile devices are the newest enterpr...
Cмотреть видео
Cмотреть видео
HD 00:01:50
Check Point: Hamas’ Cyber Tactics Exposed - Attacking IDF Soldier’s Mobile Phones
The Israeli Defense Forde uncovered a Hamas network that reached out to IDF soldiers online, sometimes in romantic ways, and ask them to download applications that would infect them with Trojan horse viruses. The applications used by Hamas ...
Cмотреть видео
Cмотреть видео
HD 00:02:07
Check Point: R80 Enhances Efficiency at the University of Kansas
The University of Kansas tested R80 security management and liked what they saw. Today they enjoy increased operational efficiency through concurrent administration capabilities, APIs for automation and a single pane of glass.
Cмотреть видео
Cмотреть видео
HD 00:02:11
Check Point: R80 Streamlines Security Management at Appvion | Data Center Security
Appvion, a manufacturer of specialty papers, tested R80 security management during development and now uses it every day to gain efficiency, high visibility and concurrent management capabilities.
Cмотреть видео
Cмотреть видео
00:01:43
Check Point: Guerra cibernÌ©tica, nuestro paÌ_s es vulnerable a ataques en la red
Juan Rivera, Gerente Regional de Cono Sur
Cмотреть видео
Cмотреть видео
HD 00:14:16
Check Point: Mal uso de las redes sociales Programa DÌ_a a DÌ_a Teleamazonas, Ecuador
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
00:21:22
Check Point: Vicente Amozurrutia Director MÌ©xico de en TV Azteca Noticias
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
00:08:04
Check Point: Juan Rivera, habla sobre seguridad en redes sociales
Juan Rivera, Gerente Regional de Cono Sur
Cмотреть видео
Cмотреть видео
HD 00:03:39
Check Point: Presentan lo ̼ltimo en seguridad informatica, Cloud Computing y VirtualizaciÌ_n
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
00:06:57
Check Point: Jorge Steinfeld, Software; Entrevista en RPP TV
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео