Безопасность
218 роликов  Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
 Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных. Предотвращение утечки данных, DLP
Обеспечение информационной безопасности, борьба с киберпреступностью. ИТ-безопасность.
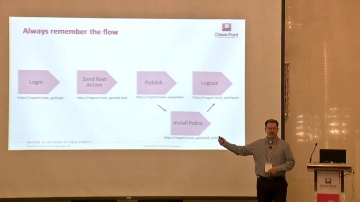
Check Point: R80 X Workflow, API, and Automation Use Cases
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
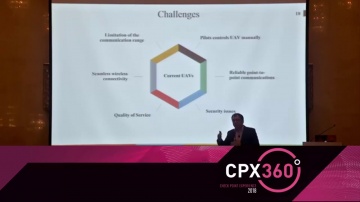
Check Point: Adaptive Security Framework for Internet of Drones
Internet of Drones is an architecture designed for providing coordinated access to controlled airspace for Unmanned aerial vehicles (UAVs).
Cмотреть видео
Cмотреть видео
Check Point: IoT & Industrial Cyber Attacks - Myth or Reality?
There is a lot of hype around how IoT will be able to change our lives, make us smarter, more efficient and more connected than ever. On the other end some site the potential danger this revolution will bring assuming IoT will not be arch...
Cмотреть видео
Cмотреть видео
Check Point: Latest Innovations in Cyber Defense
In this session, we are going to see and use the latest protections from SandBlast Network and SandBlast Agent against the recent strains of malware and security risks from 2017.
Cмотреть видео
Cмотреть видео
Check Point: Learn from the Masters: Maximize the value of your Threat Prevention
Would you like to use SandBlast like a Cyber Jedi? Find out how to achieve the best possible prevention and visibility utilizing the full power of SandBlast’s cutting-edge cyber technologies. Learn from our top experts' cool tricks and be...
Cмотреть видео
Cмотреть видео
Check Point: Artificial Intelligence in Managed Incident Response
The presentation is focused on the Managed Incident Response 5.(MIR) and it will be based on the case studies of our two award-winning** customer projects, ITC and GSTN. We have successfully executed & extended the Sandblast Solution to ...
Cмотреть видео
Cмотреть видео
Check Point: Centralized Security Management Across the Enterprise
Managing security means having to deal with multiple point solutions. This is not only a challenge from an operations/TCO perspective, but also from a security standpoint (point solutions versus a consolidated approach will create security...
Cмотреть видео
Cмотреть видео
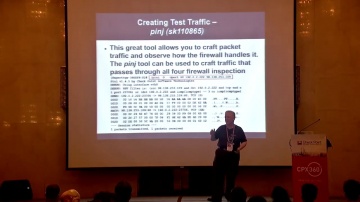
Check Point: Best of CheckMates: My Top CLI Commands
This presentation will highlight the most useful CLI commands submitted via CheckMates by real users just like you!+ For more information: Use cases, examples and case studies will be presented for the top CLI commands from the CheckMate...
Cмотреть видео
Cмотреть видео
Check Point: vSEC on AWS Cloud Use Case and Best Practices
Moving computing resources and data to public clouds means security responsibilities become shared between you and your cloud provider. While infrastructure protection is delivered by the provider, customers are responsible for protecting ...
Cмотреть видео
Cмотреть видео
Check Point: Automating the Rulebase
From beginning to scripting, learn how to get started and automate common tasks in the rule base using R80.10 and common scripting/orchestration tools. Get the tools needed and learn some orchestration tips from 's automation experts
Cмотреть видео
Cмотреть видео
Check Point: Building a Secure Platform as CIO - CPX 360 Keynote
In his keynote, Sharon Schusheim will discuss what it takes to build and operate a secure platform as a CIO. For more information: CPX 360 promises to be the premier cyber security summit. For the first time, we will bring our customers...
Cмотреть видео
Cмотреть видео
Check Point: Ask Me Anything - How to Sell to a CISO
In this fireside chat with Jerry Pitman, CISO, Tenneco , will share what he looks for when meeting with security vendors and also the less effective sales pitches he experienced
Cмотреть видео
Cмотреть видео
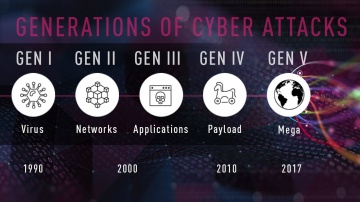
Check Point: Gen V Cyber Security with Moti Sagey - CPX 360
In his keynote, Moti Sagey will discuss in a pragmatic fact based way what it takes to build a Gen V security solution and how the cyber landscape matches the must have for effective security.
Cмотреть видео
Cмотреть видео
Check Point: Architecting Consolidated Security with Infinity
Presenting The Good, The Bad and The Ugly. Where does your company’s architecture fit? Learn how to build the best Infinity architecture and chime into a live interview listening to those who have transformed Ugly into Good.
Cмотреть видео
Cмотреть видео
Check Point: Gil Shwed Awarded 2018 Israel Prize For Technology & Innovation
Credit to Israeli Broadcasting Service, Kann News 2018 Gil Shwed CEO of software was recently awarded the Israel Prize for Technology & Innovation. The video shows Gil Shwed accepting the award and also details Gil Shwed's journey as an e...
Cмотреть видео
Cмотреть видео
Check Point: Top Cloud Cyber Security Challenges in 2018
Head of Product Marketing, Data Center and Cloud, Don Mayer, discusses some of the top cyber security challenges organizations face with the cloud in 2018. He dives into the amount of cyber attacks or cyber threats targeting the cloud and e...
Cмотреть видео
Cмотреть видео
Check Point: 2018 Cyber Security - 5TH GENERATION CYBER ATTACKS
The 5th Generation of Cyber Attacks is here, is your Cyber Security ready in 2018? Darrell Burkey, Director of IPS Products interviews with WADK-AM in Newport/ Providence areas in Rhode Island on Gen V cyber security. Visit - to learn more ...
Cмотреть видео
Cмотреть видео
Check Point: CloudGuard SaaS Demo Series: Protecting Sensitive Data
For more information: Watch this short demonstration video to learn how CloudGuard SaaS, an industry-first software-as-a-service (SaaS) security solution, provides advanced security and sensitive data protection for SaaS applications such ...
Cмотреть видео
Cмотреть видео
Check Point: Zero-day Threat Protection for SaaS Email | CloudGuard SaaS Demo
Demo showing how CloudGuard Saas provides advanced security and threat prevention for SaaS applications. For more information: Watch this short demonstration video to learn how CloudGuard SaaS, an industry-first software-as-a-service (Saa...
Cмотреть видео
Cмотреть видео
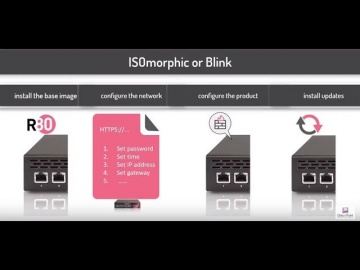
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
Check Point: Without the Best Security, Bad Things Happen
Two chatty security guards get distracted by a shiny coin, and their VIP client is swept away by criminals in a white van. For more information visit Takes real life security scenario, and demonstrates how the standard, traditional methods ...
Cмотреть видео
Cмотреть видео
Check Point: How to Hack a Cell Phone | Demo for Understanding Mobile Security
Want to hack a Smartphone? A hands-on approach to understanding mobile security. Learn more here: Ever wanted to know how to hack a smartphone? Join this exciting live demo to see first-hand how easy it is! Learn more:
Cмотреть видео
Cмотреть видео
Check Point: New Cyber Security Technologies and Cyber Threat Solutions
is your partner against cyber-crime. This is realized on a daily basis by thousands of customers worldwide using the most advanced cyber security technologies. More information: These technologies are part of Infinity’s cyber security a...
Cмотреть видео
Cмотреть видео
Check Point: Microsoft Azure and CloudGuard - Intelligent Cloud Security - CPX 360 2018
In his keynote, Avi Ben Menahem, Director of Azure Security Microsoft will discuss what it takes to build and operate a secure cloud platform, the approach the team at Microsoft takes to secure Azure, and the importance of a strong develope...
Cмотреть видео
Cмотреть видео
Check Point: Hacking the Boardroom - CPX 360 2018
Cybersecurity is a boardroom discussion for enterprise corporations globally. In this fun & entertaining presentation, you will learn how to approach senior executive for an effective discussion on Cybersecurity & how the Internet of Everyt...
Cмотреть видео
Cмотреть видео
Check Point: Internet of Things: The Dangers of IoT - CPX 360 2018
The concept of Internet of Things (IoT) truly represents a radical shift in how companies will operate, governments will govern and individuals will live their lives. Micro compute technologies and autonomous systems will permeate our day-t...
Cмотреть видео
Cмотреть видео
Check Point: Cyber Threat Incident Response War Stories
The Cloud is an amazing game changer. It provides the ability to revolutionize IR. But it can also have a much darker side. Join the head of the Cyber Threat Incident Response Team as we explore the darker side of the Cloud and provide...
Cмотреть видео
Cмотреть видео
Check Point: How to Hack a Smartphone - Demo with Pablo Perez CPX 360
Ever wanted to know how to hack a smartphone? Join this exciting live demo to see first-hand how easy it is. For more information visit In this session, Michael Shaulov will demonstrate a live hacking of a smartphone. After the demonstrat...
Cмотреть видео
Cмотреть видео
Check Point: Cyber Security Trends, Jeff Schwartz - CPX 360 2018, Why Our Security Problems are Gett
Security spending is up 8% year over year, yet security incidents are up ~40%. Why does the security "ball of yarn" continue to unravel as we pull the string. In this session, you will learn why our security problems continue to get worse ...
Cмотреть видео
Cмотреть видео
Check Point: Cyber Security Trends: Thierry Karsenti - CPX 360 2018
Security spending is up 8% year over year, yet security incidents are up ~40%. Why does the security "ball of yarn" continue to unravel as we pull the string. In this session, you will learn why our security problems continue to get worse ...
Cмотреть видео
Cмотреть видео