Безопасность
218 роликов  Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
 Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных. Предотвращение утечки данных, DLP
Обеспечение информационной безопасности, борьба с киберпреступностью. ИТ-безопасность.
О ключевых параметрах организации работы ситуационного центра ИБ (SOC) в компании
В рамках видео мы расскажем о ключевых параметрах, которые необходимо определить для организации работы ситуационного центра ИБ (SOC) в компании. Рассмотрен вопрос о создании сценариев выявления инцидентов ИБ с учетом актуальных для компани...
Cмотреть видео
Cмотреть видео
Средство контроля за действиями привилегированных пользователей SafeInspect
SafeInspect является полнофункциональным российским решением для контроля привилегированных учетных записей и сессий в современных информационных системах. Предлагаем вам обзор продукта.Спикер: Сергей Шерстюк, Менеджер по развитию продуктов...
Cмотреть видео
Cмотреть видео
Практические особенности внедрения систем класса DLP - Вебинар Романа Ванерке
В рамках вебинара "Практические особенности внедрения систем класса DLP" мы расскажем об особенностях внедрения систем класса DLP, обсудим ошибки допускаемые заказчиками при внедрении средств защиты от утечки информации и как их можно избеж...
Cмотреть видео
Cмотреть видео
Ксения Засецкая - Управление инцидентами информационной безопасности от А до Я
Управление инцидентами информационной безопасности один из ключевых процессов, направленный на снижение размера потенциального ущерба от реализации угроз. На вебинаре рассмотрены ключевые этапы создания и внедрения процессов управления инци...
Cмотреть видео
Cмотреть видео
«ДиалогНаука»: Управление инцидентами информационной безопасности от А до Я
Управление инцидентами информационной безопасности один из ключевых процессов, направленный на снижение размера потенциального ущерба от реализации угроз информационной безопасности. На вебинаре будут рассмотрены ключевые этапы создания и в...
Cмотреть видео
Cмотреть видео
Вебинар по вопросам практической реализации требований законодательства «О персональных данных»
Мы провели очередной вебинар по вопросам практической реализации требований законодательства «О персональных данных». Тема очень живая.На вебинаре мы затронули такие интересные вопросы как:- проблемы и сложности, с которыми вы столкнулись п...
Cмотреть видео
Cмотреть видео
ДиалогНаука: Стандарт Банка России СТО БР ИББС-1.0
В рамках вебинара представлена информация о произошедших изменениях законодательства РФ в сфере обеспечения информационной безопасности в организациях банковской системы Российской Федерации СТО БР ИББС-1.0-2004.Спикер: Антон Свинцицкий, ру...
Cмотреть видео
Cмотреть видео
Cybertinel: Защита инфраструктуры от уязвимостей нулевого дня
«Астерос Информационная безопасность» предлагает решение для защиты инфраструктуры заказчика от уязвимостей «нулевого дня» и расследования хакерских атак с помощью технологий ведущего израильского производителя Cybertinel. Включите рус...
Cмотреть видео
Cмотреть видео
Аладдин Р.Д.: Битва за Telegram: отключат ли в России интернет?
Битва за Telegram: отключат ли в России интернет?
Cмотреть видео
Cмотреть видео
Аладдин Р.Д.: Эксперт о технической стороне вопросов, связанных с Telegram
Радио "Коммерсант FM", апрель, 2018 Экспертный комментарий Алексея Гришина, руководителя отдела информационных технологий "Аладдин Р.Д."
Cмотреть видео
Cмотреть видео
Код Безопасности: Защита жизненного цикла данных с помощью Secret Net Studio
Компания «Код Безопасности» основана в 2008 году и ведет свою деятельность на основании девяти лицензий ФСТЭК России, ФСБ России и Министерства обороны Российской Федерации. Российский разработчик программных и аппаратных средств защиты ...
Cмотреть видео
Cмотреть видео
Код Безопасности: Порядок подключения к АС СЭП
Компания «Код Безопасности» основана в 2008 году и ведет свою деятельность на основании девяти лицензий ФСТЭК России, ФСБ России и Министерства обороны Российской Федерации. Российский разработчик программных и аппаратных средств защиты ...
Cмотреть видео
Cмотреть видео
Код Безопасности: ПАК «Соболь» 4.0: Новые возможности четвертого поколения АПМДЗ
Компания «Код Безопасности» основана в 2008 году и ведет свою деятельность на основании девяти лицензий ФСТЭК России, ФСБ России и Министерства обороны Российской Федерации. Российский разработчик программных и аппаратных средств защиты инф...
Cмотреть видео
Cмотреть видео
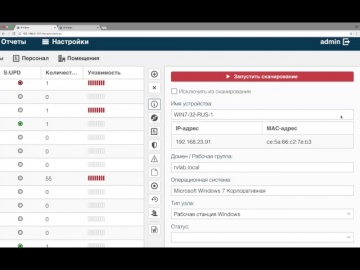
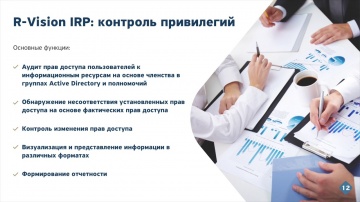
Привилегии пользователей
Видео-обзор функционала «Привилегии пользователей» платформы R-Vision.Возможность инвентаризации привилегий пользователей на основании данных учетных записей в Active Directory. Эта опция позволяет автоматически выявлять пользователей с пра...
Cмотреть видео
Cмотреть видео
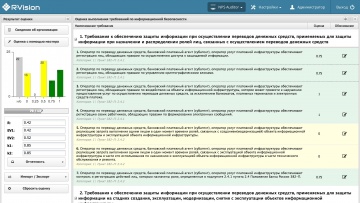
R-Vision: NPS Auditor (самооценка по требованиям 382-П, 3007-У)
R-Vision: NPS Auditor - модуль оценки соответствия требованиям 382-П и подготовки отчетности для Центрального Банка
Cмотреть видео
Cмотреть видео
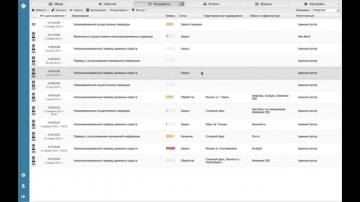
Ролик IRP
Краткий обзор R-Vision Incident Response Platform – платформы автоматизации деятельности по мониторингу, регистрации и реагированию на инциденты информационной безопасности.
Cмотреть видео
Cмотреть видео
Видео_Инструкция по работе с модулем NPS Auditor
В данном видео показаны основные шаги по проведению оценки соответствия информационной безопасности (при осуществлении переводов денежных средств) требованиям Положения 382-П с использованием модуля NPS Auditor
Cмотреть видео
Cмотреть видео
Обзор пакета обновления R-Vision: Incident Manager 1.5
Данный пакет обновлений содержит следующие изменения: Добавлена возможность импортировать данные по инцидентам из файлов KliKO. В форму редактирования события включены поля даты и времени завершения событияВнесены коррективы в форму Сводног...
Cмотреть видео
Cмотреть видео
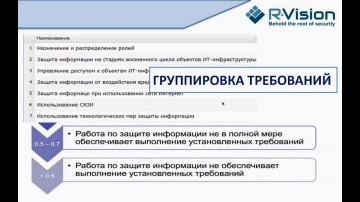
Вебинар: Проведение оценки соответствия требованиям 382-П с помощью R-Vision (12 сентября 2013 г.)
Из вебинара вы узнаете: - последние изменения в составе требований согласно указанию 3007-У - особенности использования режима оценки с использованием мастера в RVision: NPS Auditor - некоторые особенности оценки требований, определенных...
Cмотреть видео
Cмотреть видео
Обзор обновления R-Vision: Compliance Manager 1.3
Обзор обновления R-Vision: Compliance Manager 1.3
Cмотреть видео
Cмотреть видео