Видео
7128 роликов  В этом разделе собраны экспертные видеоматериалы, посвященные полному циклу создания программных продуктов. Мы разбираем не только актуальные стеки технологий, но и методологии управления разработкой в условиях цифровой ...
В этом разделе собраны экспертные видеоматериалы, посвященные полному циклу создания программных продуктов. Мы разбираем не только актуальные стеки технологий, но и методологии управления разработкой в условиях цифровой ...
 В этом разделе собраны экспертные видеоматериалы, посвященные полному циклу создания программных продуктов. Мы разбираем не только актуальные стеки технологий, но и методологии управления разработкой в условиях цифровой ...
В этом разделе собраны экспертные видеоматериалы, посвященные полному циклу создания программных продуктов. Мы разбираем не только актуальные стеки технологий, но и методологии управления разработкой в условиях цифровой ... Разработка ПО и приложений
Видеокаталог 12N
Check Point: Malware Protection 2018 - Public Health Service Prevents, Not Just Detects, Advanced Th
For more information: Malware Protection in 2018 is about prevention not just detection. As a leading West Coast provider of emergency health services, this Public Health Service organization has over two million patients and runs over...
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
Check Point: The Mississippi Secretary of State & CTO Prevents Ransomware
For more information visit Seeking to modernize its security infrastructure, the Mississippi Secretary of State upgraded to SandBlast and now prevents ransomware attacks and enjoys a peace of mind.
Cмотреть видео
Cмотреть видео
Check Point: What is CheckMates?
For more information: A brief introductory video about 's official user community: CheckMates!
Cмотреть видео
Cмотреть видео
Диасофт: FLEXTERA Credit Workflow for Seamless Customer Experience
FLEXTERA Credit Workflow is a complex suite of software components designed to support all steps of the loan origination process both for corporate and individual customers.
Cмотреть видео
Cмотреть видео
About Neomatica company - manufacturer of ADM devices for satellite monitoring of objects
Neomatica is a designer and manufacturer of ADM equipment, which is the basis of an effective control system for any moving and stationary object.
Cмотреть видео
Cмотреть видео
DATA MINER: Carlos León - The future is now: join the DevOps revolution!
DevOps Pro Moscow 2017 - Conference for Developers and IT Professionals. November 16, 2017 |
Cмотреть видео
Cмотреть видео
Check Point: Deploy Small Business Appliances with the Zero Touch Cloud Service
Watch our overview of the Zero Touch Cloud Service to see how you can save valuable time in the initial deployment of our small business security appliances. For more information:
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
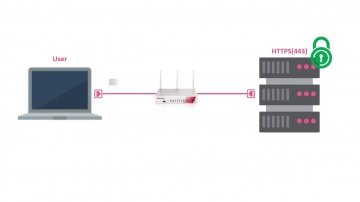
Check Point: HTTPS Inspection on Small Business Appliances
Watch our tutorial on how to enable HTTPS inspection on our 700 Appliance to improve your small business security. More information:
Cмотреть видео
Cмотреть видео
Check Point: Trial Threat Emulation on Small Business Appliances
Watch our tutorial on how to trial Threat Emulation (sandboxing) on our 700 Appliance URL for more information:
Cмотреть видео
Cмотреть видео
Check Point: CAN News, Colin Pennan talks on 'Advanced Persistent Threats'
For More Information Visit: Advanced Persistent Threats are not your average cyber-threat . Learn what makes "Advanced Persistent Attacks" unique and the intricate planning goes into these targeted attacks. In this interview Colin P...
Cмотреть видео
Cмотреть видео
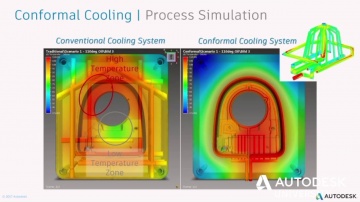
Повышение инновационности проектов с помощью предварительных виртуальных испытаний
Секция "Цифровое производство" Повышение инновационности проектов с помощью предварительных виртуальных испытаний. Adams Vince С помощью предварительных виртуальных испытаний конструкторы и инженеры по всему миру способны выбирать наилучш...
Cмотреть видео
Cмотреть видео
Искусственный интеллект и большие данные в строительстве
Секция “Технологии создания объектов будущего” Искусственный интеллект и большие данные в строительстве. Larrick Jeff Как собирать со стройки большие объемы данных и эффективно работать с ними? Эксперты Autodesk расскажут о примерах испол...
Cмотреть видео
Cмотреть видео
Check Point: Research Finds AliExpress Vulnerability: How It Works
To Read The Full Story Visit: Researchers at discovered that criminals have a new way to trick online shoppers via the massively popular AliExpress shopping portal using Java Script. After discovering the vulnerability, they immediate...
Cмотреть видео
Cмотреть видео
Check Point: R80.10 Logs and Monitor Pane – Key Components and Operations video
In this movie, we elaborate on the key components and operations of events management and reporting, within ’s R80.10 suite.
Cмотреть видео
Cмотреть видео
Renga BIM: ArchiViz - Augmented Reality (Jig) - видео
ArchiViz - Augmented Reality (Jig)
Cмотреть видео
Cмотреть видео
GroupIB: Threat Intelligence rated by Gartner, IDC, Forrester
Prevent cyber attacks with Threat Intelligence — an effective tool to counter against targeted attacks and data breaches as well as effectively manage information security risks. Group-IB is a leading cyber threat intelligence provide...
Cмотреть видео
Cмотреть видео
Check Point: Migrating from R77.3O to R80.10 Using Advanced Upgrade Procedure
This video demonstrates advanced upgrade of a real customer database from R77.30 to R80.10.
Cмотреть видео
Cмотреть видео
Renga BIM: What is Renga Architecture? Live DEMO - видео
Webinar for Structurama https://structurama.ru/?lang=en 10/27/2017. You can download trial version here: http://rengabim.com/en/download-trial/
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
DATA MINER: Accessibility Testing Techniques, Issues and Tricks by Jurij Nesvat
In this talk, Jurij will cover the accessibility testing techniques and the lessons learned, based on the projects done for a large financial institution. Jurij will also focus on why and how we improve on the issue as well as give practica...
Cмотреть видео
Cмотреть видео
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: The Mississippi Secretary of State was spending a lot of time remediating attacks on the endpoint. Seeking to enhance endpoint security, the agency adopted Sand...
Cмотреть видео
Cмотреть видео
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: Concerned about mounting advanced threats, the mississippi Secretary of state adopts SandBlast. Just 2 days after deployment, SandBlast prevents a ransomware at...
Cмотреть видео
Cмотреть видео
Check Point: Upgrading from R77.3O to R80.10 Via CPUSE
This video demonstrates in-place upgrade of a real customer database from R77.30 to R80.10 via CPUSE interface in the Web UI.
Cмотреть видео
Cмотреть видео
Check Point: Denham Capital Enjoys Agility and Security in the vSEC Protected Microsoft Azure Cloud
More information: A leading private equity firm with great success in the often unpredictable energy industry, Denham Capital needed to move to the cloud for increased agility without compromising security. With Microsoft Azure and vSEC ...
Cмотреть видео
Cмотреть видео
Check Point: Denham Capital Secures Cloud, Gains Visibility
More information: A leading private equity firm with great success in the often unpredictable energy industry, Denham Capital needed to move to the cloud without compromising performance or security. With vSEC, Denham found a solution to...
Cмотреть видео
Cмотреть видео
Check Point: Step-By-Step Guide for Securing a Web Server on Azure using CloudGuard IaaS (prev. vSE
Learn to create and deploy a web server on top of Azure public cloud and to securely publish it through a vSEC standalone server. More information:
Cмотреть видео
Cмотреть видео
Check Point: Software’s vSEC Cloud Security featured in Globb TV Interview at VMWorld 2017
More information: Itai Greenberg, Head of Cloud Security at Software Technologies, describes how ’s vSEC Cloud Security protects workloads in public clouds like AWS, private clouds like VMware SDDC ( using NSX ) and hybrid clouds built u...
Cмотреть видео
Cмотреть видео
Check Point: Defeats Mobile Cyberattacks
Advanced cybercrimes aren’t science fiction; they’re real – and have real consequences. is at the forefront of mobile security, ensuring that devices and data everywhere remain safe. We don’t just build cutting edge technology: we stand be...
Cмотреть видео
Cмотреть видео