Поиск по тегу «threat prevention» в разделе Видеокаталог
HD 00:03:07
Check Point: Customer Success: AlmavivA Group
Almaviva, Italy's number one Information & Communication Technology provider, describes how Technologies protects the organizations infrastructure.
Cмотреть видео
Cмотреть видео
HD 00:01:48
Check Point: Mobile Security: Capsule
Introducing Capsule – Your Complete Secure Mobility Solution. Learn More: Only provides ONE solution that addresses ALL your mobile security needs: Protect devices (smartphones, tablets, and laptops) from threats everywhere, establish a...
Cмотреть видео
Cмотреть видео
HD 00:01:58
Check Point: Threat Prevention: Receives Top Marks For Zero-Day Malware Block Rates
In a world of ever-changing cyber threats, organizations are facing the unprecedented growth of unknown malware. These attacks focus on stealing data, sabotaging business continuity, or damaging a company’s reputation. To protect against th...
Cмотреть видео
Cмотреть видео
HD 00:04:19
Check Point: Analyst, Third Party Testing Validations 2014
Learn More: is excited to have received top awards from respected industry sources and certification bodies for its Next Generation Firewall, IPS and Threat Prevention Appliance products.
Cмотреть видео
Cмотреть видео
HD 00:01:44
Check Point: Customer & Partner Insights- California DMV
partners with hundreds of companies across the U.S. and internationally to form long-term business and person relationships. To learn more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as they share w...
Cмотреть видео
Cмотреть видео
HD 00:05:24
Check Point: : Introducing Software-defined Protection | Cyber Security Software
To address today’s EVER-CHANGING threat landscape, has introduced a MODULAR and dynamic security architecture that envisions a THREE-LAYER infrastructure that provides operational RESILIENCE and real-time, PROACTIVE protection.
Cмотреть видео
Cмотреть видео
HD 00:04:19
Check Point: SMB Cyber Security - 600 Appliance Setup
Small businesses need cost-effective security that provides robust protections and ease of use. For more information: brings its long-standing history of security expertise to a range of solutions optimized for the unique demands of smal...
Cмотреть видео
Cмотреть видео
HD 00:05:29
Check Point: Next Generation Firewall, How To Choose The Right One | Network Security
What questions should you ask when choosing the right network security protection in an integrated next generation firewall platform? For more information: provides customers of all sizes with the latest data and network security protect...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео
HD 00:15:01
Check Point: Do You Know What's Hiding On Your Network?
This video summarizes the analysis and findings in the 2013 Security Report. For more information: provides organizations of all sizes with the latest data and network security protection in an integrated next generation firewall platfo...
Cмотреть видео
Cмотреть видео
HD 00:15:01
Check Point: Do You Know What's Hiding On Your Network?
This video summarizes the analysis and findings in the 2013 Security Report. For more information: provides organizations of all sizes with the latest data and network security protection in an integrated next generation firewall platfo...
Cмотреть видео
Cмотреть видео
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:04:08
Check Point: ThreatCloud | Complete Cyber Security Intelligence Infrastructure | Network Security
For more information: Introducing ThreatCloud, the first collaborative network to fight cyber-attacks.
Cмотреть видео
Cмотреть видео
HD 00:04:23
Check Point: SmartEvent | Security Management Walk-Through
Are you tired of managing security by manually searching through millions of logs to find the information you need? There is a better way! Watch this SmartEvent Video to learn how to manage your security more efficiently. For more informa...
Cмотреть видео
Cмотреть видео
HD 00:03:04
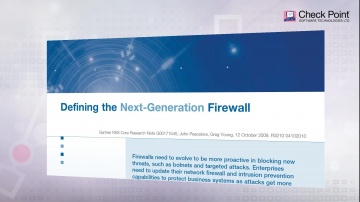
Check Point: Choosing the Right Next Generation Firewall | NGFW Explained
For more information: What is a Next Generation Firewall, where did the term come from and why is leading this market.
Cмотреть видео
Cмотреть видео
HD 00:03:20
Check Point: Third Party Security Validation | Threat Prevention
For more information: is excited to have received top awards from respected industry sources and certification bodies for its Next Generation Firewall, IPS and Threat Prevention Appliance products.
Cмотреть видео
Cмотреть видео
HD 00:07:07
Check Point: Compliance Software Blade Demonstration
Introduction and overview to the Compliance Software Blade and its features and functions.For more information: The Compliance Software Blade monitors your management, Software Blades and security gateways to constantly validate that you...
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: 2013 Security Report | Cyber Security
Based on research of nearly 900 companies and 120,000 hours of monitored traffic, the 2013 Security Report reveals major security risks organizations are exposed to on a daily basis. For information: Most importantly, the report provides...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: DDoS Protector - Technical Overview | DDoS Protection
's new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: This innovative solution quickly inspects suspicious files, emulates how they run to discover mali...
Cмотреть видео
Cмотреть видео
00:05:02
Check Point: on National Czech Republic Television
Eurograbber was launched against banking customers, using a sophisticated combination of malware directed at computers and mobile devices. For more information click here: The malware, in conjunction with the attackers' command and contr...
Cмотреть видео
Cмотреть видео
HD 00:04:43
Check Point: Next-Generation Secure Web Gateway | Network Security
Learn More: Are you trying to secure Web 2.0 with 1.0 tools? The Web has evolved, threats have evolved, so should your Web Security! In this video, learn how to best protect against today's web-borne malware and help businesses to get th...
Cмотреть видео
Cмотреть видео
HD 00:04:05
Check Point: Denial of Service Attacks & How to Protect Against Them
DDoS Protector™Appliances block Denial of Service attacks within seconds with multi-layered protection and up to 40 Gbps of performance. For more information: Alon Kantor, Corporate Development Architect at talks about the threat of dist...
Cмотреть видео
Cмотреть видео
HD 00:03:18
Check Point: Advanced Network Security: New Anti-Bot Software Blade
Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention. More information: provides organizations of all sizes with the latest data and network security protection i...
Cмотреть видео
Cмотреть видео
00:01:45
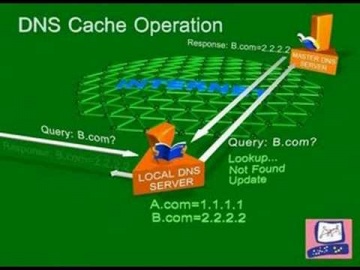
Check Point: DNS Cache Poisoning Attack | Internet Security
Software explains common DNS attacks. Learn More: DNS is the glue that holds the Internet, including web and e-mail together. A successful attack may severely impact the availability of an organization’s public facing web sites and e-mail...
Cмотреть видео
Cмотреть видео