Поиск по тегу «check point» в разделе Видеокаталог
HD 00:20:10
Код ИБ: Check Point. Итоги 2020 года - видео Полосатый ИНФОБЕЗ
Итоги 2020 года компании Check Point в интервью с главой представительства Василием Дягилевым. ⌚ Таймкоды выпуска: 00:00 Вступление 00:23 Успехи и достижения года 06:23 Влияние пандемии на компанию 12:18 Опыт 2020 года 15:30 Планы на 2021 ...
Cмотреть видео
Cмотреть видео
HD 01:17:14
Код ИБ: Промышленная кибербезопасность | Безопасная среда - видео Полосатый ИНФОБЕЗ
Бесперебойная работа по-прежнему остается приоритетом промышленных предприятий, что требует повышенного внимания к кибербезопасности АСУ ТП. Как обеспечивать должный уровень кибербезопасности промышленных систем, учитывая в том числе и тре...
Cмотреть видео
Cмотреть видео
HD 01:20:52
Код ИБ: Защита мобильных устройств | Безопасная среда - видео Полосатый ИНФОБЕЗ
Переход на удаленку ознаменовался еще более активным использованием личных мобильных устройств в корпоративных целях. Как сделать так, чтобы такое использование было не только удобным, но и безопасным? Об этом, и не только, поговорим с эк...
Cмотреть видео
Cмотреть видео
HD 00:21:38
Код ИБ: Разделение ответственности в облаках. Взгляд со стороны Check Point - видео Полосатый ИНФОБЕ
Разделение ответственности в облаках. Взгляд со стороны Check Point Амир Алиев. Инженер по безопасности, Check Point Облачные провайдеры предоставляют множество инструментов для обеспечения безопасности. Какие из них стоит использовать? ...
Cмотреть видео
Cмотреть видео
HD 01:21:18
Код ИБ: Безопасность облаков | Безопасная среда - видео Полосатый ИНФОБЕЗ
На первый взгляд может показаться, что для обеспечения безопасности в облаке подходят те же методы, что и в традиционных ИТ-средах, но это не так. Что именно нужно защищать, если мы говорим о безопасности облаков, за что должен отвечать про...
Cмотреть видео
Cмотреть видео
HD 00:18:09
Разработка iot: Эра Интернета вещей. Зачем нужен Check Point NGFW для IoT? - видео
О безопасности IOT рассказывает Дмитрий Кудра, консультант по информационной безопасности Check Point
Cмотреть видео
Cмотреть видео
HD 01:12:00
Что нового в R81 Management?
Никита Турков рассказывает об изменениях и новом функционале в управлении R81 - единой платформе кибезбезопасности.Вопросы, обсуждаемые в этом вебинаре: - Профили Infinity Treat Prevention - Объекты Data Center Query - Новая NAT полит...
Cмотреть видео
Cмотреть видео
HD 00:23:27
Экспо-Линк: Защита веб приложения в два клика: WAF как автоматическое искусство
Защита веб приложения в два клика: WAF как автоматическое искусство Валерий Денисов Архитектор по облачной безопасности, Check Point#БезопаснаяСреда #WAF #CheckPoint #codeibКОД ИБ: семейство проектов, главная миссия которых — делать м...
Cмотреть видео
Cмотреть видео
HD 00:25:24
Infinity SOC - true XDR - видео
Infinity SOC - true XDR Сергей Забула, Channel SE Team Leader, Check Point Никита Турков, Security Engineer, Check Point #БезопаснаяСреда #SOC #CheckPoint #codeibКОД ИБ: семейство проектов, главная миссия которых — делать мир информац...
Cмотреть видео
Cмотреть видео
HD 01:21:37
Код ИБ: Безопасная среда | Безопасная разработка - видео Полосатый ИНФОБЕЗ
Современные подходы к разработке диктуют высокие требования к безопасности. Особенно важно быстро и без отрыва от производства выявлять и устранять уязвимости. В теории все понятно, а вот на практике не все так просто. Как сделать свой проц...
Cмотреть видео
Cмотреть видео
HD 00:17:39
Код ИБ: Kubernetes, lambda, публичные облака и контейнеры – как обеспечить безопасность со всех стор
Валерий Денисов Security Engineer, Check Point #БезопаснаяСреда #БезопаснаяРазработка #codeib #CheckPoint КОД ИБ: семейство проектов, главная миссия которых — делать мир информационной безопасности простым и понятным Здесь вы об...
Cмотреть видео
Cмотреть видео
HD 00:25:18
Check Point и DevSecOps: безопасность в новой эре разработки ПО
Микросервисы, контейнеры, Kubernetes, DevOps, DevSecOps – эти термины все прочнее входят в нашу жизнь. Даже самые консервативные организации начинают использовать такие технологии. А многие уже в полной мере вкусили их преимущества. Но к...
Cмотреть видео
Cмотреть видео
HD 00:29:35
CloudGuard IaaS: динамическая сетевая безопасность в отечественных и зарубежных облаках - ви
Амир Алиев, консультант по информационной безопасности, Check Point Software Technologies Задействовав ресурсы публичного облака у вас может возникнуть вопрос - где здесь безопасность и кто за нее отвечает? а докладе вы узнаете ответ на эт...
Cмотреть видео
Cмотреть видео
HD 00:27:13
iot: Безопасная экосистема Интернета вещей (IoT) - видео
Do you trust your IoT devices? Itzik Feiglevitch, Product Manager, Check Point Software TechnologiesРастущие с экспоненциальной скоростью устройства Интернета вещей приносят значительную ценность бизнесу, развивая и расширяя его возможности...
Cмотреть видео
Cмотреть видео
HD 03:01:29
GIS Days 2020 | PRO 2 - видео
PRO 2. Мониторинг КИИ: SOC для АСУ ТП. Обнаружение аномалий в сетях АСУ ТП с использованием методов машинного обучения. 22 октября 2020 года состоялась традиционная конференция по информационной безопасности «Global Information Security Da...
Cмотреть видео
Cмотреть видео
HD 00:57:30
Информационная безопасность бизнеса: от осознания - к работающим механизмам
Крупномасштабные кибератаки наносят значительный экономический ущерб, сокращают время выпуска на рынок продуктов и услуг, снижают скорость внедрения инноваций, а также негативно сказываются на лояльности заказчиков и партнеров. И чем сложне...
Cмотреть видео
Cмотреть видео
HD 00:45:10
АСУ ТП: Экспертный аудит ИБ - видео
Выступление Сергея Борисова, УЦСБ 16.03.2020 на митапе по компьютерной безопасности Kuban Cyber Security Tech Talks В докладе речь идет о наиболее экспертной части комплексного аудита ИБ, в рамках которой производится анализ соответствия ...
Cмотреть видео
Cмотреть видео
HD 00:02:52
Expo-Link: Код ИБ 2018 | Калининград
Нужно быть готовым к новым неизвестным угрозам 29 ноября Калининград впервые встречал самую масштабную конференцию по информационной безопасности «Код ИБ». Более 120 профессионалов в сфере ИТ и ИБ собралось в зале отеля Mercure Kaliningrad...
Cмотреть видео
Cмотреть видео
00:05:44
Код ИБ: #разговорыпроИБ №1: Сергей Чекрыгин, Check Point - видео Полосатый ИНФОБЕЗ
Почему нужно следить за регуляторами, как с появлением больших данных можно по-новому взглянуть на утечки, что делать с интернетом вещей и почему надо смотреть на то, что делается в мире. Об этом в выпуске #1 с Чергеем Чекрыгиным, менеджер...
Cмотреть видео
Cмотреть видео
HD 00:18:35
Check Point: CheckMates TechTalk: Analysis of SiliVaccine
SiliVaccine is an Anti-Virus tool used in North Korea. Security Researchers at got a copy of it to see if it had any abnormal behavior or undocumented features. Sure enough, it did!
Cмотреть видео
Cмотреть видео
HD 00:02:44
Check Point: You Asked, CEO Gil Shwed Answers!
Is Gil Shwed a morning person or a night owl? CEO Gil Shwed talks about his favorite apps, drones, future roadmap, and recognizes the winners in our CheckMates Birthday Awards!
Cмотреть видео
Cмотреть видео
HD 00:14:41
Check Point: CheckMates TechTalk: Remote Code Execution Vulnerability on LG Smartphones
Neatsun Ziv and Jonathan Shimonovich discuss our recent publication of vulnerabilities that reside in the default keyboard of all mainstream LG smartphone models. More details:
Cмотреть видео
Cмотреть видео
HD 00:02:47
Check Point: You Asked, VP of Products Dorit Dor Answers!
Is Dr. Dorit Dor a morning person or a night owl? Our VP of Products talks about her favorite apps, drones, future roadmap, and recognizes the winners in our CheckMates Birthday Awards!
Cмотреть видео
Cмотреть видео
HD 00:01:46
Check Point: CheckMates First Birthday Award Winners
CheckMates, the user community for customers and partners, is celebrating it's first birthday by recognizing excellent contributors and content!
Cмотреть видео
Cмотреть видео
HD 00:08:24
Check Point: Lightboard Series: Dynamic Revisions
This video elaborates on the logic behind the R80.10 Security Management architecture focusing on the dynamic revisions feature. This feature automatically stores the full history of database changes, with very little footprint, consuming ...
Cмотреть видео
Cмотреть видео
HD 00:02:38
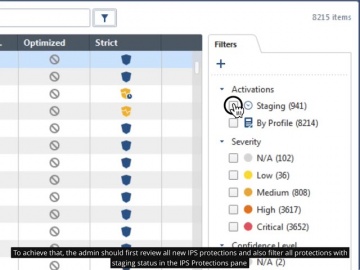
Check Point: R80.10 Policy Management – IPS Protections in Detect (Staging) State
This video elaborates on the logic behind new IPS protections status after IPS update operation and introduces best practice on changing the status of detect-staging on prevent when enough information was gathered regarding the new IPS prot...
Cмотреть видео
Cмотреть видео
HD 00:01:38
Check Point: CloudGuard SaaS Demo Series: Identity Protection for Office 365
Watch this short demonstration video to learn how CloudGuard SaaS, an industry-first software-as-a-service (SaaS) security solution, provides advanced security and identity protection including account takeover protection for SaaS applicat...
Cмотреть видео
Cмотреть видео
00:04:43
Check Point: Founder & CEO Gil Shwed on CNBC Squawk Box
CNBC Squawk Box featured Check Point CEO & Founder Gil Shwed. Gil Shwed discusses 5th generation cyber attacks. For more https://www.checkpoint.com/gen-v-cybe...Talking about level three attacks, level four attacks; what are fifth and s...
Cмотреть видео
Cмотреть видео
HD 01:01:35
Check Point: EU GDPR Webinar Replay
The European Union’s General Data Protection Regulation (‘GDPR’) poses the biggest change to the regulatory landscape of data privacy. To learn more visit: GDPR places significant policy and technical responsibilities on ANY organization ...
Cмотреть видео
Cмотреть видео
HD 00:30:26
Check Point: Who's Responsible for your Cloud Security?
A full breakdown of what is shared responsibility and the layers of security needed to protect you from security breaches in the cloud. For more information:
Cмотреть видео
Cмотреть видео