Код ИБ: Безопасная среда | Threat Intelligence - видео Полосатый ИНФОБЕЗ → Похожие видео ролики , Страница 26
Любой компании важно выстраивать операционную деятельность ИБ-подразделения, а также внедрять и реализовывать защитные меры, ориентируясь на полную картину угроз, а не вслепую. В этом значительно может помочь использование threat intelligence. Почему threat intelligence пока не сильно распространен и как с его помощью начать понимать ландшафт угроз для прогнозирования возможных атак и реализации адекватных мер защиты? Эти вопросы, и не только, обсудим с экспертами в рамках нашего онлайн-проекта Код ИБ | БЕЗОПАСНАЯ СРЕДА. #БезопаснаяСреда #ThreatIntelligence #codeib КОД ИБ: семе...
Подробнее в видео...
Подробнее в видео...
HD 00:29:43
Check Point: The Mobile Threat Landscape
From Judy to Blueborne, the proliferation of mobile threats has grown rapidly in the past year. In this session, we review the various types of mobile threats, how they spread and the damage they cause. We will also be providing practical ...
Cмотреть видео
Cмотреть видео
HD 00:02:20
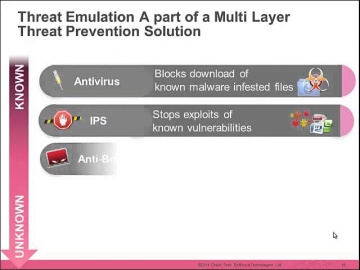
Check Point: Trial Threat Emulation on Small Business Appliances
Watch our tutorial on how to trial Threat Emulation (sandboxing) on our 700 Appliance URL for more information:
Cмотреть видео
Cмотреть видео
HD 00:33:25
Check Point: Learn from the Masters: Maximize the value of your Threat Prevention
Would you like to use SandBlast like a Cyber Jedi? Find out how to achieve the best possible prevention and visibility utilizing the full power of SandBlast’s cutting-edge cyber technologies. Learn from our top experts' cool tricks and be...
Cмотреть видео
Cмотреть видео
HD 00:19:59
Check Point: Cyber Threat Incident Response War Stories
The Cloud is an amazing game changer. It provides the ability to revolutionize IR. But it can also have a much darker side. Join the head of the Cyber Threat Incident Response Team as we explore the darker side of the Cloud and provide...
Cмотреть видео
Cмотреть видео
HD 00:31:45
Check Point: Artificial Intelligence in Managed Incident Response
The presentation is focused on the Managed Incident Response 5.(MIR) and it will be based on the case studies of our two award-winning** customer projects, ITC and GSTN. We have successfully executed & extended the Sandblast Solution to ...
Cмотреть видео
Cмотреть видео
HD 00:27:48
Check Point: New Cyber Security Technologies and Cyber Threat Solutions
is your partner against cyber-crime. This is realized on a daily basis by thousands of customers worldwide using the most advanced cyber security technologies. More information: These technologies are part of Infinity’s cyber security a...
Cмотреть видео
Cмотреть видео
HD 00:04:47
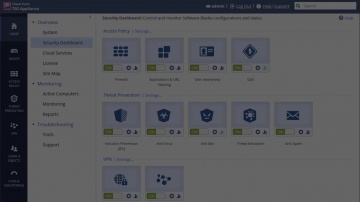
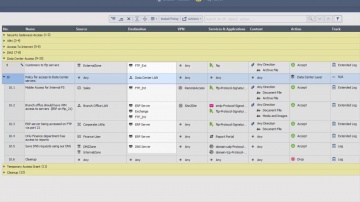
Check Point: R80.10 SmartConsole Security Policies View | Threat Prevention
This video is an overview that describes important features and functionality of the R80.10 SmartConsole and focuses on: Unified Access and Threat Prevention Policies Example of inline layers for zone-based policy Using multiple blades in o...
Cмотреть видео
Cмотреть видео
HD 00:01:18
Check Point: RSA 2016: Mobile Threat Prevention | Mobile Security
For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:02:42
Check Point: SandBlast Cloud Advanced Threat Prevention for Microsoft Office 365 | Email Security
Dramatic growth in the use of cloud-based email for the enterprise brings with it an array of security risks, including susceptibility to sophisticated cyber attacks such as ransomware and APTs which use email as a primary entry point. San...
Cмотреть видео
Cмотреть видео
HD 00:02:48
Check Point: Samsung Research America Chooses Mobile Threat Prevention
As the research arm of an industry-leading manufacturer of consumer electronics, Samsung Research America is committed to forward-looking innovation and bringing new products to market ahead of competitors. More Info: The last thing it n...
Cмотреть видео
Cмотреть видео
HD 00:02:43
Check Point: Introduces Next-Generation Threat Prevention Appliances | Advanced Threat Prevention
Introducing the next-generation of appliances designed to unleash the full power of advanced threat prevention security for businesses of all sizes. For more information visit: Gen V Cyber Security is here: Infinity is the first conso...
Cмотреть видео
Cмотреть видео
HD 00:02:07
Check Point: Advanced Endpoint Protection & Forensics | Advanced Threat Prevention
Continuously preventing even the most sophisticated cyber attacks and responding quickly to limit damages on endpoint devices is essential to all businesses today. More information: The SandBlast Agent extends Ûªs industry-leading zero-...
Cмотреть видео
Cмотреть видео
00:36:06
Check Point: The Security Zone Ep. 3: How to Choose Your Next Generation Threat Emulation Solution
Organizations are facing unprecedented growth in the number of security threats from malware. New attack types combine known and unknown threats to exploit vulnerabilities. Join us to learn how can protect against unknown malware.
Cмотреть видео
Cмотреть видео
00:06:54
Check Point: CAN News, Colin Pennan talks on 'Advanced Persistent Threats'
For More Information Visit: Advanced Persistent Threats are not your average cyber-threat . Learn what makes "Advanced Persistent Attacks" unique and the intricate planning goes into these targeted attacks. In this interview Colin P...
Cмотреть видео
Cмотреть видео
HD 00:03:03
Check Point: Koch Media Crushes Advanced Attacks with SandBlast | Advanced Threat Prevention
Koch Media develops games globally, which is a process fraught with peril to the intellectual property in their games. Koch sought to replace Cisco and decided on SandBlast Zero DayProtection to crush advanced attacks. For more informat...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Hackers constantly modify their strategies and techniques to evade detection by traditional sandboxes to reach corporate resources. For more information visit: SandBlast Zero-Day Protection, with evasion-resistant malware detection, pro...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: CPU-level Sandboxing with SandBlast | Advanced Threat Prevention
s cutting-edge CPU-level inspection engine eliminates cyber threats at the point of pre-infection before cyber attack. VLearn more: This unrivaled exploit prevention technology provides a higher catch rate of threats and gives organizati...
Cмотреть видео
Cмотреть видео
HD 00:38:04
Check Point: Identifying The Best Sandboxing Solution Featuring Miercom | Advanced Threat Prevention
Learn More: Protecting against known, and new, advanced, unknown threats requires the most rapid and precise detection and protection technologies. With multiple solutions available, finding the best one can be challenging. Independent te...
Cмотреть видео
Cмотреть видео
HD 00:03:30
Check Point: Tutorial: Configuring IPS Settings with R80 Security Management Server | Advanced Threa
How to use R80 SmartConsole to configure the settings for the IPS Software Blade. For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:21:37
Check Point: Artificial Intelligence: a Silver Bullet in Cyber Security? CPX 360 Keynote
Artificial Intelligence is the Industrial Revolution of our time. It is already reshaping our world and is likely to transform practically every facet of our human lives. Learn more here: Fighting cybercrime is one of its many application...
Cмотреть видео
Cмотреть видео
HD 00:04:02
Check Point: SideStepper: Anatomy of an iOS Vulnerability | Mobile Threat Prevention
For more information, visit: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: disclosed details about SideStepper, a vulnerability that can be used to install malicious enterprise apps o...
Cмотреть видео
Cмотреть видео
HD 00:02:50
Check Point: Threat Emulation Protects Investment Firm: Gimv
Learn More: Gimv, a leading European private equity and venture capital investment company, leverages ThreatCloud Emulation technology to prevent against zero day attacks. Watch as IT Manager Kristof Poppe discusses his experience wi...
Cмотреть видео
Cмотреть видео
00:46:00
Check Point: Tackling a Complex Threat Landscape with Software-defined Protection
Description: In this 30-minute webinar we'll examine software-defined protection (SDP). This new architecture addresses today's security challenges by providing operational resilience and real-time, proactive protection. You'll learn: • ...
Cмотреть видео
Cмотреть видео
HD 00:01:25
Check Point: R80 Security Management | Advanced Threat Prevention
's R80 Security Management helps you consolidate security functions so you can be more efficient and effective at deploying the strongest protections across your organization. More Information:
Cмотреть видео
Cмотреть видео
HD 00:02:17
Check Point: Big Bad Mobile Threats of 2015 - Mobile Threat Prevention
The mobile threat landscape changed dramatically in 2015. Simple hacks and rudimentary malware was quickly replaced by sophisticated cyber thieves who know exactly what sensitive data they can take from you and how. Along with the growing s...
Cмотреть видео
Cмотреть видео
HD 00:03:43
Check Point: The Threat of Bots and Botnets | IoT | Network Security
Learn More: explains: What is a bot? What is a botnet? What is an Advance Persistent Threat?
Cмотреть видео
Cмотреть видео
HD 00:20:42
Check Point: Microsoft Azure and CloudGuard - Intelligent Cloud Security - CPX 360 2018
In his keynote, Avi Ben Menahem, Director of Azure Security Microsoft will discuss what it takes to build and operate a secure cloud platform, the approach the team at Microsoft takes to secure Azure, and the importance of a strong develope...
Cмотреть видео
Cмотреть видео
HD 00:02:29
Check Point: 24/7 Protection with ThreatCloud Managed Security Service | Threat Prevention
For more information visit ThreatCloud Managed Security Service is a cloud-based service providing actionable attack alerts for IPS, Anti-Bot and Antivirus customers. experts remotely monitor, manage and escalate attack incidents. Custo...
Cмотреть видео
Cмотреть видео
HD 00:03:39
Check Point: Mobile Threat Prevention Demo - Malware Invasion on an iOS Device
In this video, demonstrates an end-to-end threat and remediation situation on an iOS device using Mobile Threat Prevention. To learn more about Mobile Threat Prevention for iOS and Android devices, visit Report: IDC Technology Spotligh...
Cмотреть видео
Cмотреть видео
HD 00:02:45
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Learn how to take the first steps to enable your security gateway to leverage the SandBlast Cloud Service or the SandBlast Appliance. Learn more at: See what end users would experience, and what security administrators can expect to see. ...
Cмотреть видео
Cмотреть видео