PLM: ЛОЦМАН:PLM Управление архивом - видео → Похожие видео ролики , Страница 64
Вся разработанная на предприятии документация подлежит учету и хранению, которыми занимаются специалисты службы архива или бюро технической документации. На вебинаре демонстрируется как автоматизировать эти процессы в системе ЛОЦМАН:PLM с помощью прикладного модуля. Модуль ЛОЦМАН:PLM Архив позволяет вести электронную картотеку документов и абонентов, обеспечивает быстрый доступ к документам с учетом назначенных прав пользователя, а также предоставляет возможность обмена документацией с другими предприятиями. В программе: 0:00 - Вводная часть 3:40 - Основные возможности и новинк...
Подробнее в видео...
Подробнее в видео...
00:05:37
Check Point: Why Trust Matters for Security
Following a press round table event held in London in December 2012, panelists looked at why trust is fundamental to security, and how organizations can prove that they and their employees can be trusted. The spokespeople are: - Kevin B...
Cмотреть видео
Cмотреть видео
HD 00:01:22
Check Point: Stopping The Next Cyber Attack | Threat Prevention
Understanding your exposure to threats—and what you can do about it is not only responsible business management—it’s critical to business survival. Turn Security into an Enabler, Not a Disabler. offers network infrastructure security, ant...
Cмотреть видео
Cмотреть видео
HD 00:00:47
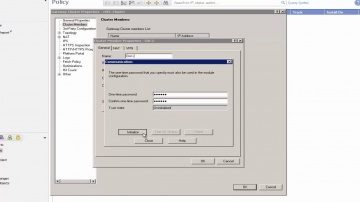
Check Point: 06 Creating a vSEC Gateway IP Address Pool
We recommend that you create pool for automatic assignment of management interface IP addresses.
Cмотреть видео
Cмотреть видео
HD 00:01:15
Check Point: Advanced Cyber Attack Business Protection
SandBlast mobile offers the best advanced cyber attack protection for your business. More information: Cybercriminals are better than ever at stealing sensitive information from your smartphone or tablet. Whether it's personal information...
Cмотреть видео
Cмотреть видео
HD 00:00:43
Check Point: Customer Quote: ThreatCloud Emulation Discovers and Prevents Zero-Day Attacks
Gimv IT Manager Kristof Poppe comments on 's Threat Emulation and zero day attacks.
Cмотреть видео
Cмотреть видео
HD 00:03:04
Check Point: Choosing the Right Next Generation Firewall | NGFW Explained
For more information: What is a Next Generation Firewall, where did the term come from and why is leading this market.
Cмотреть видео
Cмотреть видео
HD 00:01:32
Check Point: 07 Deploying the Service
This procedure uses an Agent VM, for an environment with a local Datastore. If you will use an external Datastore, have its details ready before you begin.
Cмотреть видео
Cмотреть видео
HD 00:14:29
Check Point: Radio Interview Discussing 2013 Cyber Security Threats
Kellman Meghu, Head of Security Engineering at speaks to The Biggs Radio Show about what cyber security threats we should look out for in 2013
Cмотреть видео
Cмотреть видео
HD 00:00:27
Check Point: Customer Quote: ThreatCloud Emulation Integrated into Software Blade Architecture
Gimv IT Manager Kristof Poppe comments on 's ThreatCloud Emulation integrated into the Software Blade Architecture for layered security.
Cмотреть видео
Cмотреть видео
HD 00:02:05
Check Point: Secure your Mobile Phone Now | Introducing SandBlast Mobile
Protecting your enterprise from mobile threats and cyber attacks. More information: Worried about your Mobile Privacy? Secure your mobile phone now against mobile threats. Keeping your business safe from cyberattacks is no easy task, and...
Cмотреть видео
Cмотреть видео
HD 00:03:49
Check Point: A Day in the Life of Mike, a Next Generation Firewall Administrator
For more information: See how security admins can easily create granular policies—based on users or groups—to identify, block or limit usage of over Web 2.0 applications and educate users on safe Internet use with our Next Generation Fire...
Cмотреть видео
Cмотреть видео
HD 00:01:45
Check Point: Preventing Tomorrow's Cyber Security Threats
Increasing your enterprise security often means increasing your complexity and management challenges in kind. For more information, visit Growing complexity in security infrastructure puts a huge strain on the efficiency of the security o...
Cмотреть видео
Cмотреть видео
HD 00:01:51
Check Point: 08 Creating Security Group and IP Sets
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
HD 00:04:43
Check Point: Next-Generation Secure Web Gateway | Network Security
Learn More: Are you trying to secure Web 2.0 with 1.0 tools? The Web has evolved, threats have evolved, so should your Web Security! In this video, learn how to best protect against today's web-borne malware and help businesses to get th...
Cмотреть видео
Cмотреть видео
HD 00:02:10
Check Point: SandBlast Mobile: Protecting Against Malicious Apps
Our mobile devices are used for both personal and business purposes. Installing new apps may compromise both your private and corporate data. Every year, malicious apps downloaded from official app stores infect millions of mobile devices....
Cмотреть видео
Cмотреть видео
HD 00:00:40
Check Point: Customer Quote: Industry Leading NGFW Performance with Integrated Management
Gimv IT Manager Kristof Poppe comments on 's industry leading next generation firewall performance with integrated management.
Cмотреть видео
Cмотреть видео
HD 00:04:19
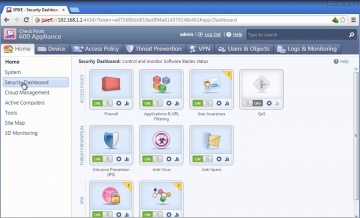
Check Point: 600 Appliance Setup
Watch our tutorial on how to setup our 600 Appliance, 's latest edition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:08:41
Check Point: 's Avi Rembaum: Shedding Light on the Dark Web
Leveraging intelligence culled from the Dark Web will help boost information security for enterprises, says Avi Rembaum of Software Technologies. "What's really becoming far more important is leveraging the intelligence coming from that r...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: DDoS Protector - Technical Overview | DDoS Protection
's new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: This innovative solution quickly inspects suspicious files, emulates how they run to discover mali...
Cмотреть видео
Cмотреть видео
HD 00:02:28
Check Point: 09 Creating vSEC Cluster Objects
Create a cluster object, with vSEC Gateway members. Each gateway will automatically get the license attached to the cluster.
Cмотреть видео
Cмотреть видео
HD 00:05:30
Check Point: Denial of Service Cyber Attack Protector Overview
DDoS Protector™Appliances block Denial of Service attacks within seconds with multi-layered protection and up to 40 Gbps of performance. For more information: Modern DDoS attacks use new techniques to exploit areas where traditional secu...
Cмотреть видео
Cмотреть видео
HD 00:03:07
Check Point: Customer Success: AlmavivA Group
Almaviva, Italy's number one Information & Communication Technology provider, describes how Technologies protects the organizations infrastructure.
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: SandBlast Mobile: How It Works
Accurate threat detection is a critical component of preventing advanced attacks on smartphones and tablets. Traditional mobile anti-virus, signature-based solutions identify known threats, but they can't detect zero-day malware or apps tha...
Cмотреть видео
Cмотреть видео
HD 00:02:20
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: The Mississippi Secretary of State was spending a lot of time remediating attacks on the endpoint. Seeking to enhance endpoint security, the agency adopted Sand...
Cмотреть видео
Cмотреть видео
HD 00:02:13
Check Point: 10 Redirecting traffic to and installing policy
This video demonstrates how to redirect traffic to entities and then install Security policy to the vSEC cluster object.
Cмотреть видео
Cмотреть видео
HD 00:03:20
Check Point: Third Party Security Validation | Threat Prevention
For more information: is excited to have received top awards from respected industry sources and certification bodies for its Next Generation Firewall, IPS and Threat Prevention Appliance products.
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: 2013 Security Report | Cyber Security
Based on research of nearly 900 companies and 120,000 hours of monitored traffic, the 2013 Security Report reveals major security risks organizations are exposed to on a daily basis. For information: Most importantly, the report provides...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: Partner Insights: Nathan Browne, Director of Technical Services, Access IT Group
Find out more: Access IT Group's director of technical services Nathan Browne says Software-defined Protection (SDP) protects against non-previously planned for threats. Watch for more on Nathan's thoughts about SDP and what it means fo...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: Defeats Mobile Cyberattacks
Advanced cybercrimes aren’t science fiction; they’re real – and have real consequences. is at the forefront of mobile security, ensuring that devices and data everywhere remain safe. We don’t just build cutting edge technology: we stand be...
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: Concerned about mounting advanced threats, the mississippi Secretary of state adopts SandBlast. Just 2 days after deployment, SandBlast prevents a ransomware at...
Cмотреть видео
Cмотреть видео