Поиск по тегу «security (quotation subject)» в разделе Видеокаталог
HD 00:31:46
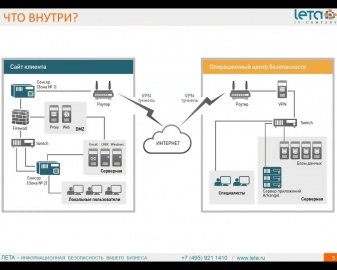
Вебинар Мониторинг информационной безопасности 24 7 2015 04 15 10 30
Видио вебинар Мониторинг информационной безопасности 24 7 2015 04 15 10 30.
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: Stop Advanced Mobile Threats Before They Start | SandBlast Mobile Security
Learn More: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: Cyber criminals may be stealing data from your smartphone or tablet without your knowledge. They’re experts at exploiting vulner...
Cмотреть видео
Cмотреть видео
HD 00:02:14
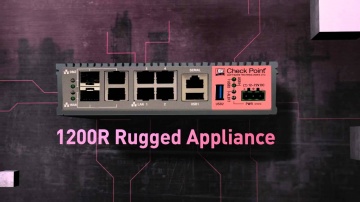
Check Point: 1200R: Ruggedized Security for Industrial Control Systems | SCADA | ICS Security
Overview of ICS and 1200R appliance:
Cмотреть видео
Cмотреть видео
HD 00:31:58
Код Безопасности: Интеграция Secret Net и ПАК «Соболь»: преимущества решения и особенности работы
Демонстрация возможностей по совместному использованию Secret Net 7 и ПАК "Соболь".
Cмотреть видео
Cмотреть видео
HD 00:38:04
Check Point: Identifying The Best Sandboxing Solution Featuring Miercom | Advanced Threat Prevention
Learn More: Protecting against known, and new, advanced, unknown threats requires the most rapid and precise detection and protection technologies. With multiple solutions available, finding the best one can be challenging. Independent te...
Cмотреть видео
Cмотреть видео
00:18:31
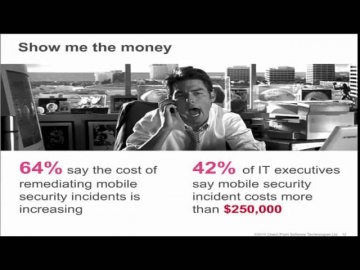
Check Point: The Security Zone Ep. 5: Impact of Mobile Devices on Information Security
teamed up with Dimensional Analysis to survey over 700 IT and security professionals in 6 countries to learn the current attitudes and trends regarding the impact of mobile devices on information security.
Cмотреть видео
Cмотреть видео
00:05:37
Check Point: Why Trust Matters for Security
Following a press round table event held in London in December 2012, panelists looked at why trust is fundamental to security, and how organizations can prove that they and their employees can be trusted. The spokespeople are: - Kevin B...
Cмотреть видео
Cмотреть видео