Поиск по тегу «sandblast» в разделе Видеокаталог
HD 00:04:49
Check Point: SandBlast Agent Forensics
This video shows SandBlast Agent’s automated forensics analysis in action. For more information: It demonstrates SandBlast Agent’s power to instantly provide security teams with a crystal-clear understanding of cyber attacks, empowering t...
Cмотреть видео
Cмотреть видео
HD 00:03:03
Check Point: Koch Media Crushes Advanced Attacks with SandBlast | Advanced Threat Prevention
Koch Media develops games globally, which is a process fraught with peril to the intellectual property in their games. Koch sought to replace Cisco and decided on SandBlast Zero DayProtection to crush advanced attacks. For more informat...
Cмотреть видео
Cмотреть видео
HD 00:02:13
Check Point: Daymark Secures Cloud with CloudGuard (formerly vSEC) for Microsoft Azure | Cloud Secur
Daymark solutions, trusted advisor to businesses in the Northeast, implemented CloudGuard (formerly vSEC) for Microsoft Azure and now recommends it to all its customers for ease of use, comprehensive visibility and threat prevention. Hea...
Cмотреть видео
Cмотреть видео
HD 00:02:13
Check Point: Daymark Secures Cloud with CloudGuard (formerly vSEC) for Microsoft Azure | Cloud Secur
Daymark solutions, trusted advisor to businesses in the Northeast, implemented CloudGuard (formerly vSEC) for Microsoft Azure and now recommends it to all its customers for ease of use, comprehensive visibility and threat prevention. Hea...
Cмотреть видео
Cмотреть видео
HD 00:01:58
Check Point: Hunze en Aa Water Resource Board enhances Network Security, SCADA Systems with SandBlas
For more information: To help ensure safe operation of its pumping stations and other key systems, the Hunze en Aa Water Resource Board implemented NGTX appliances with SandBlast zero-day protection. Through the solutions centralized mana...
Cмотреть видео
Cмотреть видео
HD 00:01:34
Check Point: DressCode Android Malware Discovered on Google Play | SandBlast Mobile Security | Andro
The mobile threat prevention research team discovered a new Android malware on Google Play, called DressCode, which was embedded into more than 40 apps, and found in more than 400 additional apps on third party app stores. notified Google...
Cмотреть видео
Cмотреть видео
HD 00:02:22
Check Point: Customer Success: Community Newspaper Group (CNG)
Watch as Infrastructure Manager, Michael Brine discusses his experience with SandBlast Agent in this customer success video. Community Newspaper Group's seventeen newspapers provide readers with the latest in local news, sports, and ente...
Cмотреть видео
Cмотреть видео
HD 00:02:07
Check Point: ゼロデイの脅威からエンドポイントを保護するSandBlast Agent
脅威の進化に伴い、組織には、あらゆるレベルで攻撃を防ぎ、迅速に対応して被害を抑えるソリューションの導入が推奨されます。SandBlast Agentは、幅広い高度なエンドポイント保護技術により、社内および社外で利用するエンドポイントを保護します。攻撃の全体像をすばやく把握できるフォレンジック分析機能も搭載しており、インシデント・レスポンス・チームの生産性を最大限に高めます。
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: SandBlast - ゼロデイ攻撃対策ソリューション
攻撃者は、検出をすり抜け企業の資産にアクセスする目的で、絶えず新たな戦略や手法を編み出しています。このような攻撃に対処するチェック・ポイントのゼロデイ攻撃対策ソリューションは、より深いレベルで検査を実施しマルウェアやゼロデイ攻撃からの保護を強化しながら、安全なコンテンツをユーザにすばやく確実に転送します。
Cмотреть видео
Cмотреть видео
HD 00:02:48
Check Point: Samsung Research America Chooses Mobile Threat Prevention
As the research arm of an industry-leading manufacturer of consumer electronics, Samsung Research America is committed to forward-looking innovation and bringing new products to market ahead of competitors. More Info: The last thing it n...
Cмотреть видео
Cмотреть видео
HD 00:02:29
Check Point: Customer Success: Community Newspaper Group (CNG)
For More Information: Community Newspaper Groups seventeen newspapers provide readers with the latest in local news, sports, and entertainment in Perth, Australia. As a publishing outlet, its critical for Community Newspaper Group to kee...
Cмотреть видео
Cмотреть видео
HD 00:04:02
Check Point: SideStepper: Anatomy of an iOS Vulnerability | Mobile Threat Prevention
For more information, visit: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: disclosed details about SideStepper, a vulnerability that can be used to install malicious enterprise apps o...
Cмотреть видео
Cмотреть видео
HD 00:01:32
Check Point: SandBlast Mobile Security: Man-in-the-Middle Mobile Attacks
Our mobile devices are more vulnerable then we think. A man-in-the middle attack is a potential threat every time you connect to a Wi-Fi network. For more information: Imagine you are at a coffee shop and you want to connect to Wi-Fi and...
Cмотреть видео
Cмотреть видео
HD 00:01:10
Check Point: RSA 2016: Prevent Cyberattacks from Entering the Endpoint with SandBlast Agent
More information:
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: CPU-level Sandboxing with SandBlast | Advanced Threat Prevention
s cutting-edge CPU-level inspection engine eliminates cyber threats at the point of pre-infection before cyber attack. VLearn more: This unrivaled exploit prevention technology provides a higher catch rate of threats and gives organizati...
Cмотреть видео
Cмотреть видео
HD 00:54:57
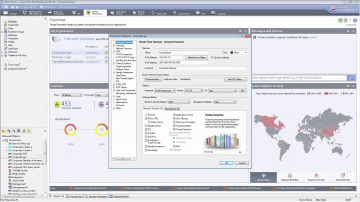
Check Point: Understanding SandBlast - Zero-Day Protection
Understanding your exposure to threats—and what you can do about it is not only responsible business management—it’s critical to business survival. More information: Turn Security into an Enabler, Not a Disabler. SandBlast Zero-Day Prote...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Hackers constantly modify their strategies and techniques to evade detection by traditional sandboxes to reach corporate resources. For more information visit: SandBlast Zero-Day Protection, with evasion-resistant malware detection, pro...
Cмотреть видео
Cмотреть видео
HD 00:02:45
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Learn how to take the first steps to enable your security gateway to leverage the SandBlast Cloud Service or the SandBlast Appliance. Learn more at: See what end users would experience, and what security administrators can expect to see. ...
Cмотреть видео
Cмотреть видео
HD 00:01:45
Check Point: Preventing Tomorrow's Cyber Security Threats
Increasing your enterprise security often means increasing your complexity and management challenges in kind. For more information, visit Growing complexity in security infrastructure puts a huge strain on the efficiency of the security o...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео