Поиск по тегу «computer security (industry)» в разделе Видеокаталог
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:04:19
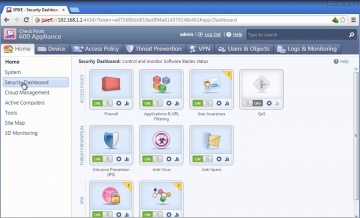
Check Point: 600 Appliance Setup
Watch our tutorial on how to setup our 600 Appliance, 's latest edition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:03:20
Check Point: Third Party Security Validation | Threat Prevention
For more information: is excited to have received top awards from respected industry sources and certification bodies for its Next Generation Firewall, IPS and Threat Prevention Appliance products.
Cмотреть видео
Cмотреть видео
HD 00:07:07
Check Point: Compliance Software Blade Demonstration
Introduction and overview to the Compliance Software Blade and its features and functions.For more information: The Compliance Software Blade monitors your management, Software Blades and security gateways to constantly validate that you...
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: 2013 Security Report | Cyber Security
Based on research of nearly 900 companies and 120,000 hours of monitored traffic, the 2013 Security Report reveals major security risks organizations are exposed to on a daily basis. For information: Most importantly, the report provides...
Cмотреть видео
Cмотреть видео
HD 00:02:14
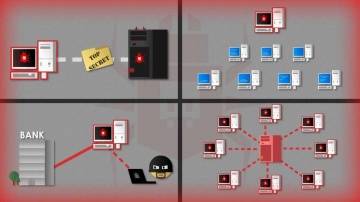
GroupIB: Group-IB Bot-Trek | Botnet Monitoring and Cyber Intelligence
Group-IB Bot-Trek™ is a real-time botnet and cyber intelligence service that provides a direct access to compromised data and helps to prevent fraud. Bot-Trek™ gathers compromised data and intelligence from botnets and computer underground...
Cмотреть видео
Cмотреть видео