Check Point: обзор и установка CloudGuard IaaS Gateway в Yandex.Cloud → Похожие видео ролики , Страница 5
В этом видео рассматриваются различные варианты продуктов Check Point CloudGuard IaaS Firewall & Threat Prevention (PAYG и BYOL) в Яндекс.Облако.Продукты Check Point в Yandex.Cloud: https://cloud.yandex.ru/marketplace?s... CloudGuard IaaS for Yandex.Cloud: http://supportcontent.checkpoint.com/... FAQ и полезные материалы: https://community.checkpoint.com/t5/R...Страница ПО R80.40 со ссылками на свежую версию SmartConsole и Jumbo Hotfix Accumulator: https://supportcontent.checkpoint.com... CloudGuard IaaS Automation for KVM Based Platforms: http://supportcontent.checkpoint.com/...Создание в...
Подробнее в видео...
Подробнее в видео...
HD 00:18:31
Check Point: Cyber Security in the Era of Exponential Technology
Amnon Bar-Lev - President, Software We are in an extraordinary time in human history. Thanks to innovative and disruptive technologies we live longer, healthier and more educated than ever before. While technologies such as cloud computin...
Cмотреть видео
Cмотреть видео
HD 00:20:00
Check Point: Cloud Security Challenges by Peter Sandkuijl - CPX 360 2018
Public and hybrid cloud adoption is exploding among enterprises, but so are cloud hacks and breaches. Cloud assets are at risk from the same types of threats targeting physical networks. What's more, cyber criminals are using increasingly...
Cмотреть видео
Cмотреть видео
HD 00:02:12
Check Point: Anatomy of a Smishing Attack: Czech Posta App
A new smishing attack targeted users in the Czech Republic was discovered January 26, 2017. Smishing, or SMS phishing, is a vector attackers use to send SMS messages from supposedly legitimate organizations. These messages persuade users t...
Cмотреть видео
Cмотреть видео
00:43:43
Check Point: Q&A: Compliance and Regulations with Jeremy Kaye | Network Security Risk and Compliance
For more information: On June 18, 2013, 's in house #regulations and #compliance expert Jeremy Kaye spoke with Dameon Welch-Abernathy live in our first Google+ Hangouts on Air. This was an opportunity to hear some of the challenges your p...
Cмотреть видео
Cмотреть видео
HD 00:01:28
Check Point: RSA 2016: R80 Security Management Launch | Security Management Software
For more information: Organizations that possess consolidated security simplify complex environments, improve efficiency and ensure security is consistently deployed across the organization. Change the way you manage security with integra...
Cмотреть видео
Cмотреть видео
HD 00:02:43
Check Point: Introduces Next-Generation Threat Prevention Appliances | Advanced Threat Prevention
Introducing the next-generation of appliances designed to unleash the full power of advanced threat prevention security for businesses of all sizes. For more information visit: Gen V Cyber Security is here: Infinity is the first conso...
Cмотреть видео
Cмотреть видео
00:04:43
Check Point: Founder & CEO Gil Shwed on CNBC Squawk Box
CNBC Squawk Box featured Check Point CEO & Founder Gil Shwed. Gil Shwed discusses 5th generation cyber attacks. For more https://www.checkpoint.com/gen-v-cybe...Talking about level three attacks, level four attacks; what are fifth and s...
Cмотреть видео
Cмотреть видео
00:05:57
Check Point: Choosing the right endpoint security solution
For more information: Fred Borjesson regional endpoint sales manager at Software Technologies discusses the best ways for enterprises to manage their endpoint security and explains the benefit of using one unique single endpoint security...
Cмотреть видео
Cмотреть видео
HD 00:19:41
Check Point: Information Security : Gioacchino Buscemi (CPX 360)
In this session, Gioacchino Buscemi, Network Security Officer, European Space Agency. will share his vision on modern IT, among others the importance of compliance and security and how they are very different. Additionally, he will review ...
Cмотреть видео
Cмотреть видео
HD 00:02:37
Check Point: Protecting Mobile Devices Together - ElevenPaths – Telefonica and | Mobile Security
“Mobile devices are critical to the way we do business today. With cyberattacks growing in sophistication and frequency, exposing both the business and personal data we store on smartphones and tablets, mobile devices are the newest enterpr...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: サンドボックス機能のカギはCPUレベルの検査とOSレベルのサンドボックス分析
チェック・ポイントのサンドボックスはCPUレベルの検査とOSレベルのサンドボックス分析を組み合わせて、危険性の高い攻撃コードやゼロデイ攻撃、標的型攻撃による感染を防ぎます。
Cмотреть видео
Cмотреть видео
HD 00:02:19
Check Point: The Mississippi Secretary of State & CTO Prevents Ransomware
For more information visit Seeking to modernize its security infrastructure, the Mississippi Secretary of State upgraded to SandBlast and now prevents ransomware attacks and enjoys a peace of mind.
Cмотреть видео
Cмотреть видео
HD 00:27:06
Check Point: Un Viaje Seguro a la Nube | CyberDay Spain 2017
Javier Hijas, Cloud Security Team Leader Europe
Cмотреть видео
Cмотреть видео
HD 00:02:22
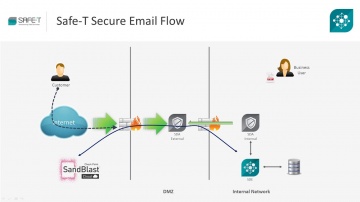
Check Point: Securing Data Exchange with SandBlast and Safe-T HDS
Organizations today face host of challenges in securing high risk data. SandBlast is most advanced protection against zero-day malware threats, while Safe-T HDS secures all data exchange scenarios including human data exchange such as secu...
Cмотреть видео
Cмотреть видео
HD 00:10:27
Check Point: L’Oréal vSEC Case Study
As one of the world’s leading beauty brands, the L'Oréal group has spent the last century in the pursuit of perfection.
Cмотреть видео
Cмотреть видео
HD 00:23:09
Check Point: R80.10 Best Practices – Migrating from R77.30
Get the insights from Professional Services on how to migrate from R77.30 to R80.10.
Cмотреть видео
Cмотреть видео
HD 00:28:51
Check Point: Top 5 Cloud Security Tips (How to Protect Your Data in the Cloud)
The era of cloud is upon us; firms of all sizes and in all walks of life are looking to leverage the agility and elasticity of cloud. But cloud carries a totally new and unique set of security challenges. In this informative and entertainin...
Cмотреть видео
Cмотреть видео
HD 00:02:27
Check Point: Upgrading from R77.3O to R80.10 Via CPUSE
This video demonstrates in-place upgrade of a real customer database from R77.30 to R80.10 via CPUSE interface in the Web UI.
Cмотреть видео
Cмотреть видео
HD 00:03:58
Check Point: Compliance Software Blade | Network Security Best Practices
For more information: This is the second video in the Compliance Software Blade Demonstration Series. This video provides insight into aligning both security and compliance to security best practices.
Cмотреть видео
Cмотреть видео
HD 00:16:07
Check Point: Moving to the Public Cloud, Securely - FireChat with AWS & Azure
More than 70% of the organizations are committed to a cloud strategy in 2017. Businesses are moving their applications to the Cloud to gain more agility and efficencies. At the same time, Cloud security remains their top concern. Customers...
Cмотреть видео
Cмотреть видео
HD 00:24:38
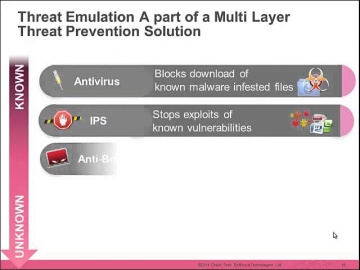
Check Point: The Security Zone Ep. 2: Forget Zero Day, Hello Zero Second
Delayed response is no longer enough to protect your business from the speed of malware. We need a ZERO SECOND response. A recent benchmark test assessed how fast Threat Emulation and other competitive products stop malware from entering a...
Cмотреть видео
Cмотреть видео
HD 00:02:07
Check Point: Advanced Endpoint Protection & Forensics | Advanced Threat Prevention
Continuously preventing even the most sophisticated cyber attacks and responding quickly to limit damages on endpoint devices is essential to all businesses today. More information: The SandBlast Agent extends Ûªs industry-leading zero-...
Cмотреть видео
Cмотреть видео
HD 00:03:09
Check Point: Happy International Women's Day 2018
The women of share the best advice they ever received in recognition of International Women's Day 2018. Learn more about at
Cмотреть видео
Cмотреть видео
00:01:34
Check Point: IPS Software Blade
SSL Certificates attacks can compromise even the most secure sites. Learn how s IPS solutions protect against this specific kind of threats.
Cмотреть видео
Cмотреть видео
HD 00:18:22
Check Point: CISO viewpoint on modern IT: Britney Hommertzheim, Director, Information Security, AMC
In this session, Britney Hommertzheim, Director, Information Security. AMC Theatres. will share his vision on modern IT, among others the importance of compliance and security and how they are very different. Additionally, he will review ...
Cмотреть видео
Cмотреть видео
HD 00:07:15
Check Point: vSEC, The Future of Cloud Security
In this video, you’ll hear from Donald Meyer, Head of Marketing, Data Center and Cloud, where he discusses issues surrounding Cloud security and how organizations can better protect themselves from vulnerabilities in the Cloud. For more in...
Cмотреть видео
Cмотреть видео
00:36:06
Check Point: The Security Zone Ep. 3: How to Choose Your Next Generation Threat Emulation Solution
Organizations are facing unprecedented growth in the number of security threats from malware. New attack types combine known and unknown threats to exploit vulnerabilities. Join us to learn how can protect against unknown malware.
Cмотреть видео
Cмотреть видео
00:06:54
Check Point: CAN News, Colin Pennan talks on 'Advanced Persistent Threats'
For More Information Visit: Advanced Persistent Threats are not your average cyber-threat . Learn what makes "Advanced Persistent Attacks" unique and the intricate planning goes into these targeted attacks. In this interview Colin P...
Cмотреть видео
Cмотреть видео
HD 00:31:09
Check Point: Security Blueprint for the Cloud Era
Discover the recommended blueprint for multi-cloud security. Take a deep dive on perimeter security, east-west security, connected clouds, auto-scale, and auto provisioning.
Cмотреть видео
Cмотреть видео
HD 00:23:46
Check Point: Choosing The Right Security Architecture | Cyber Security | Network Security
Moti Sagey - Head of Strategic Marketing & Intelligence, Software When it comes to choosing the right security architecture & security vendor, what does it take to win your trust? In this session Moti Sagey will cover three key pillars th...
Cмотреть видео
Cмотреть видео