GroupIB: Group-IB Secure Bank - client-side online fraud prevention in real time → Похожие видео ролики , Страница 8
Client-side fraud and attack prevention across sessions, platforms, and devices in real time for online & mobile banking.
Подробнее в видео...
Подробнее в видео...
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Threat Emulation Explained by | Advanced Threat Prevention
's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: 's Threat new Threat Emulation Software Blade prevents infections from undiscovered exploit...
Cмотреть видео
Cмотреть видео
HD 00:05:12
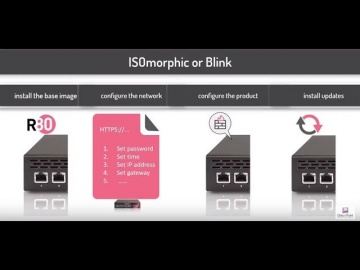
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: Stop Advanced Mobile Threats Before They Start | SandBlast Mobile Security
Learn More: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: Cyber criminals may be stealing data from your smartphone or tablet without your knowledge. They’re experts at exploiting vulner...
Cмотреть видео
Cмотреть видео
HD 00:22:53
Check Point: Gen V Cyber Security with Moti Sagey - CPX 360
In his keynote, Moti Sagey will discuss in a pragmatic fact based way what it takes to build a Gen V security solution and how the cyber landscape matches the must have for effective security.
Cмотреть видео
Cмотреть видео
HD 00:01:12
Check Point: RSA Conference 2014 - Customer Insights - Securities America, Inc.
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Leon Johnson from Securities America, Inc. speaks about the critical need to secure data in the financial industry and how integrates ...
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: Capsule Docs – Keep Your Business Documents Protected | Enterprise | Network Security
Capsule Docs protects your sensitive business documents to ensure they don’t get unintentionally exposed. See how Capsule Docs works to provide document security.
Cмотреть видео
Cмотреть видео
HD 00:01:43
Check Point: Malware Threat Prevention | Zero-Day, Zero-Second.
What can malware do in 60 seconds? One minute can change everything for a business. So what happens when the speed of business is overtaken by the speed of malware? The team devised a test to quantify that exact question. Learn More: As ...
Cмотреть видео
Cмотреть видео
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:02:44
Check Point: Protected 24x7 With | Cyber Security
For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:03:11
Check Point: Choose the Right Next Generation Firewall - Multi-Layer Security
Why Multi-Layer Security and how 's Software Blade Architecture is the most secure and scalable solution in this market. For more information: provides organizations of all sizes with the latest data and network security protection in a...
Cмотреть видео
Cмотреть видео
HD 00:01:24
Check Point: Capsule Docs - Secure Business Documents Everywhere | Network Security
Capsule Docs ensures that only authorized individuals can access your business documents. Confidently share documents with coworkers, business partners, clients, and vendors, because you are in control of their access and sharing rights.
Cмотреть видео
Cмотреть видео
HD 00:02:39
Check Point: Threat Intelligence | Threat Prevention
Learn More: In 2012, established ThreatCloud, the first collaborative security infrastructure to fight cybercrime. ThreatCloud dynamically reinforces Threat Prevention Software Blades with real-time threat intelligence derived from res...
Cмотреть видео
Cмотреть видео
HD 00:07:01
Check Point: Overview of the 61000 Appliance | Data Center Security Systems
For more information:
Cмотреть видео
Cмотреть видео
HD 00:04:08
Check Point: ThreatCloud | Complete Cyber Security Intelligence Infrastructure | Network Security
For more information: Introducing ThreatCloud, the first collaborative network to fight cyber-attacks.
Cмотреть видео
Cмотреть видео
HD 01:04:31
Check Point: Webinar replay – Auto-scale advanced security for Microsoft Azure
For more information visit: Webinar replay - hear from customer George Dialectakis, IT Consultant at Eversource Energy, on how they leverage CloudGuard IaaS advanced threat prevention security for their Microsoft Azure cloud environme...
Cмотреть видео
Cмотреть видео
HD 00:01:48
Check Point: Mobile Security: Capsule
Introducing Capsule – Your Complete Secure Mobility Solution. Learn More: Only provides ONE solution that addresses ALL your mobile security needs: Protect devices (smartphones, tablets, and laptops) from threats everywhere, establish a...
Cмотреть видео
Cмотреть видео
HD 00:01:58
Check Point: Threat Prevention: Receives Top Marks For Zero-Day Malware Block Rates
In a world of ever-changing cyber threats, organizations are facing the unprecedented growth of unknown malware. These attacks focus on stealing data, sabotaging business continuity, or damaging a company’s reputation. To protect against th...
Cмотреть видео
Cмотреть видео
HD 00:04:23
Check Point: SmartEvent | Security Management Walk-Through
Are you tired of managing security by manually searching through millions of logs to find the information you need? There is a better way! Watch this SmartEvent Video to learn how to manage your security more efficiently. For more informa...
Cмотреть видео
Cмотреть видео
00:05:37
Check Point: Why Trust Matters for Security
Following a press round table event held in London in December 2012, panelists looked at why trust is fundamental to security, and how organizations can prove that they and their employees can be trusted. The spokespeople are: - Kevin B...
Cмотреть видео
Cмотреть видео
HD 00:01:22
Check Point: Stopping The Next Cyber Attack | Threat Prevention
Understanding your exposure to threats—and what you can do about it is not only responsible business management—it’s critical to business survival. Turn Security into an Enabler, Not a Disabler. offers network infrastructure security, ant...
Cмотреть видео
Cмотреть видео
HD 00:14:29
Check Point: Radio Interview Discussing 2013 Cyber Security Threats
Kellman Meghu, Head of Security Engineering at speaks to The Biggs Radio Show about what cyber security threats we should look out for in 2013
Cмотреть видео
Cмотреть видео
HD 00:02:05
Check Point: Secure your Mobile Phone Now | Introducing SandBlast Mobile
Protecting your enterprise from mobile threats and cyber attacks. More information: Worried about your Mobile Privacy? Secure your mobile phone now against mobile threats. Keeping your business safe from cyberattacks is no easy task, and...
Cмотреть видео
Cмотреть видео
HD 00:01:51
Check Point: 08 Creating Security Group and IP Sets
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео
HD 00:04:43
Check Point: Next-Generation Secure Web Gateway | Network Security
Learn More: Are you trying to secure Web 2.0 with 1.0 tools? The Web has evolved, threats have evolved, so should your Web Security! In this video, learn how to best protect against today's web-borne malware and help businesses to get th...
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: 2013 Security Report | Cyber Security
Based on research of nearly 900 companies and 120,000 hours of monitored traffic, the 2013 Security Report reveals major security risks organizations are exposed to on a daily basis. For information: Most importantly, the report provides...
Cмотреть видео
Cмотреть видео
00:03:42
Check Point: Customer Success: The University of Liege Uses To Boost Network Security
The University of Liege in Belgium selects to help mitigate security issues around areas like BYOD and the increasing need for bandwidth. With 's 12600s and 12200s appliances in the data center and 2200s for its branch locations, the Univ...
Cмотреть видео
Cмотреть видео
HD 00:00:31
Check Point: Without the Best Security, Bad Things Happen
Two chatty security guards get distracted by a shiny coin, and their VIP client is swept away by criminals in a white van. For more information visit Takes real life security scenario, and demonstrates how the standard, traditional methods ...
Cмотреть видео
Cмотреть видео
HD 00:07:58
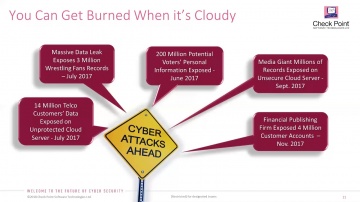
Check Point: 2017 Cyber Security Survey
Donald Meyer, Head of Marketing, Data Center and Cloud, discusses top security concerns that IT professionals have regarding Cloud and Mobility security. For more information:
Cмотреть видео
Cмотреть видео
HD 00:01:46
Check Point: Introducing ThreatCloud Emulation Services | Cloud Security
Learn More: Find Zero-Day Threats before they find you with ThreatCloud Emulation Services.
Cмотреть видео
Cмотреть видео