Digital Security: Instahook demo → Похожие видео ролики , Страница 4
Подделка screenlife. «Да я Мадонну лично знаю» - мы привыкли ставить под сомнение подлинность изображений (все в курсе возможностей фотошопа). Другое дело – видеозапись экрана устройства, ей доверия больше. Но спешим вас огорчить: чтобы подделать screenlife, не нужно ни спецэффектов, ни навыков видеомонтажа. Все что нужно, – это фреймворк инструментации Frida, небольшой скрипт на JavaScript и один ревёрсер.Это видео к статье: https://dsec.ru/blog/poddelka-screenlife-da-ya-mad...
Подробнее в видео...
Подробнее в видео...
HD 00:01:57
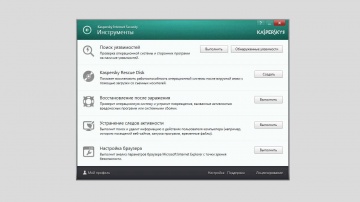
Как использовать Инструменты в Kaspersky Internet Security 2014
Мы расскажем, как в Kaspersky Internet Security 2014 использовать Поиск уязвимостей, Диск аварийного восстановления и другие Инструменты. Видеоинструкции по Kaspersky Internet Security 2014 Официальный сайт Лаборатории Касперского Чит...
Cмотреть видео
Cмотреть видео
HD 00:03:56
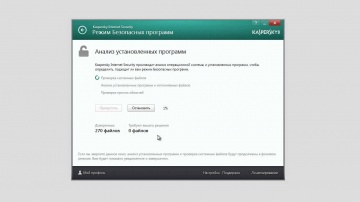
Как использовать режим Безопасных программ в Kaspersky Internet Security 2014
Если одним компьютеров пользуется много людей, и они устанавливают на него свои программы, возникает большой риск поймать вирус. В видео мы расскажем, как режим Безопасных программ в составе Kaspersky Internet Security 2014 поможет избежать...
Cмотреть видео
Cмотреть видео
HD 00:40:40
IBS: Digital journey срудника в компании будущего через призму технологий
Выступление команды Дивизиона HR-сервисов на международном саммите HR Digital 2017 на тему: Digital journey срудника в компании будущего - первого контакта до момента найма, обучения и удержания - через призму технологий.
Cмотреть видео
Cмотреть видео
HD 00:10:56
Диасофт: Премьера «FLEXTERA Digital: посмотрите, как это работает!» на Retail Finance Forum 2015
Александр Генцис, член cовета директоров компании «», рассказывает об инновационной платформе FLEXTERA Digital на Retail Finance Forum.
Cмотреть видео
Cмотреть видео
HD 00:07:15
IBS: Digital journey срудника в компании будущего через призму технологий (коркая версия)
Выступление команды Дивизиона HR-сервисов на международном саммите HR Digital 2017 на тему: Digital journey срудника в компании будущего - первого контакта до момента найма, обучения и удержания - через призму технологий. Коркая версия
Cмотреть видео
Cмотреть видео
HD 00:42:30
DATA MINER: Michal Buczko - Automated Security Scanning in Payment Card Industry
Software Testing & QA Conference -
Cмотреть видео
Cмотреть видео
HD 00:04:41
Check Point: 700 Appliance Setup | SMB Cyber Security
For more information: Watch our tutorial on how to setup our 700 Appliance, 's latest addition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:22:35
Check Point: Architecting Consolidated Security with Infinity
Presenting The Good, The Bad and The Ugly. Where does your company’s architecture fit? Learn how to build the best Infinity architecture and chime into a live interview listening to those who have transformed Ugly into Good.
Cмотреть видео
Cмотреть видео
HD 00:01:25
Check Point: Advanced Cyber Security for 2018 | Infinity
Learn more at Introducing Infinity, the world’s most advanced cyber security and management architecture. Infinity consolidates security across network, cloud and mobile, keeping you secured from known and unknown threats, today and in ...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: 700 Series Appliances for Small Business - Product Video | SMB Cyber Security
As a small business, your focus is on building unique products, driving sales, and providing excellent service to your customers. Security is important but it seems like every week there is some new piece of software or equipment to prote...
Cмотреть видео
Cмотреть видео
HD 00:19:34
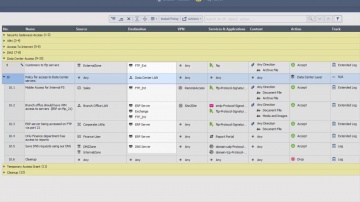
Check Point: Centralized Security Management Across the Enterprise
Managing security means having to deal with multiple point solutions. This is not only a challenge from an operations/TCO perspective, but also from a security standpoint (point solutions versus a consolidated approach will create security...
Cмотреть видео
Cмотреть видео
HD 00:34:55
Check Point: Gil Shwed Keynote: Stepping Up to Gen V of Cyber Security
Gil Shwed's keynote from CPX 2018 on the future of Cyber Security. Find out what Gen V Cyber Attacks are and how you can prevent the next Cyber Attack. For more information visit -
Cмотреть видео
Cмотреть видео
HD 00:04:30
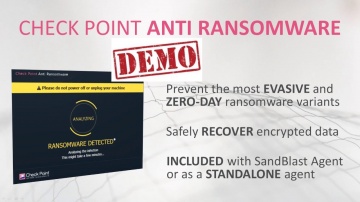
Check Point: Anti-Ransomware: Solution Brief & Demo | Tech Bytes
Anti-Ransomware protects against sophisticated zero-day ransomware. It is included in SandBlast Agent. More information: Protect endpoints from sophisticated attacks and zero-day threats, enabling a deep understanding of security events f...
Cмотреть видео
Cмотреть видео
HD 00:01:55
Check Point: Optimizes Security with Gigamon’s Full Network Visibility
and Gigamon’s joint solution provides comprehensive network visibility, optimal performance and advanced threat prevention capabilities. For more information:
Cмотреть видео
Cмотреть видео
00:01:45
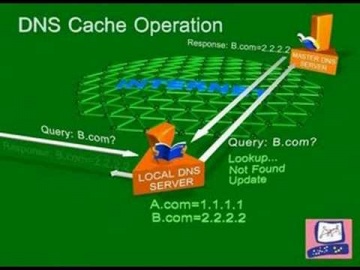
Check Point: DNS Cache Poisoning Attack | Internet Security
Software explains common DNS attacks. Learn More: DNS is the glue that holds the Internet, including web and e-mail together. A successful attack may severely impact the availability of an organization’s public facing web sites and e-mail...
Cмотреть видео
Cмотреть видео
HD 00:30:06
Check Point: SMB Security Unique Challenges
The Small and Medium Business market has the same security challenges as larger enterprises. What they don't have a lot of is time or money.
Cмотреть видео
Cмотреть видео
HD 00:17:04
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
HD 00:30:26
Check Point: Who's Responsible for your Cloud Security?
A full breakdown of what is shared responsibility and the layers of security needed to protect you from security breaches in the cloud. For more information:
Cмотреть видео
Cмотреть видео
HD 00:24:49
Check Point: Welcome to the Future of Cyber Security | Infinity
The future of cyber security is here. Learn and stay protected against today's cyber threat landscape. For more information: We are all living in a connected world which is affecting every aspect of our lives. In the past couple of ye...
Cмотреть видео
Cмотреть видео
HD 00:26:30
Check Point: Infinity | The Cyber Security Architecture of the Future
Gabi Reish - VP, Product Management and Product Marketing, Software For more information on the Cyber Security Architecture of the Future, please go to:
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
HD 00:27:48
Check Point: New Cyber Security Technologies and Cyber Threat Solutions
is your partner against cyber-crime. This is realized on a daily basis by thousands of customers worldwide using the most advanced cyber security technologies. More information: These technologies are part of Infinity’s cyber security a...
Cмотреть видео
Cмотреть видео
HD 00:02:14
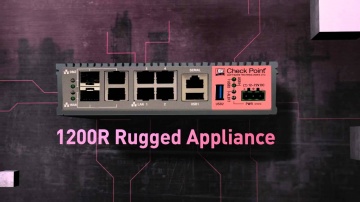
Check Point: 1200R: Ruggedized Security for Industrial Control Systems | SCADA | ICS Security
Overview of ICS and 1200R appliance:
Cмотреть видео
Cмотреть видео
HD 00:23:38
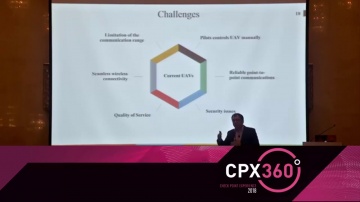
Check Point: Adaptive Security Framework for Internet of Drones
Internet of Drones is an architecture designed for providing coordinated access to controlled airspace for Unmanned aerial vehicles (UAVs).
Cмотреть видео
Cмотреть видео
HD 00:17:15
Check Point: Infinity - A Day in the Life of a Security Administrator
Having worked with access control as a basic security level for over 20 years, the speakers reminisce about how much better it was in the past.
Cмотреть видео
Cмотреть видео
HD 00:04:47
Check Point: R80.10 SmartConsole Security Policies View | Threat Prevention
This video is an overview that describes important features and functionality of the R80.10 SmartConsole and focuses on: Unified Access and Threat Prevention Policies Example of inline layers for zone-based policy Using multiple blades in o...
Cмотреть видео
Cмотреть видео
HD 00:02:49
Check Point: Advanced Cyber Security for 2018 | Prevent Gen V Cyber Attacks with Infinity
More information: ... Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the fut...
Cмотреть видео
Cмотреть видео
HD 00:01:18
Check Point: RSA 2016: Mobile Threat Prevention | Mobile Security
For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:21:03
Check Point: Cyber Security Trends, Jeff Schwartz - CPX 360 2018, Why Our Security Problems are Gett
Security spending is up 8% year over year, yet security incidents are up ~40%. Why does the security "ball of yarn" continue to unravel as we pull the string. In this session, you will learn why our security problems continue to get worse ...
Cмотреть видео
Cмотреть видео
HD 00:03:20
Check Point: 2017 Mobile Security Media Tour
Our Michael Shaulov, Head of Product, Mobile Security discusses the importance of mobile security and common vulnerabilities and threats mobile data of individuals and the enterprise. For more information:
Cмотреть видео
Cмотреть видео