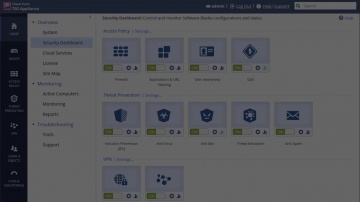
Check Point: Overview of the 61000 Appliance - with Japanese subtitles → Похожие видео ролики
HD 00:07:01
Check Point: Overview of the 61000 Appliance | Data Center Security Systems
For more information:
Cмотреть видео
Cмотреть видео
HD 00:04:41
Check Point: 700 Appliance Setup | SMB Cyber Security
For more information: Watch our tutorial on how to setup our 700 Appliance, 's latest addition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: 700 Series Appliances for Small Business - Product Video | SMB Cyber Security
As a small business, your focus is on building unique products, driving sales, and providing excellent service to your customers. Security is important but it seems like every week there is some new piece of software or equipment to prote...
Cмотреть видео
Cмотреть видео
HD 00:02:20
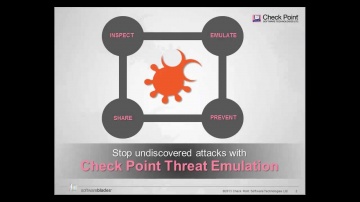
Check Point: Trial Threat Emulation on Small Business Appliances
Watch our tutorial on how to trial Threat Emulation (sandboxing) on our 700 Appliance URL for more information:
Cмотреть видео
Cмотреть видео
HD 00:06:37
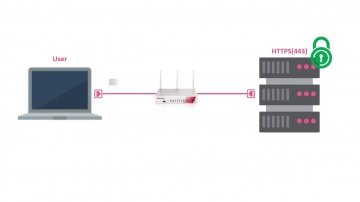
Check Point: HTTPS Inspection on Small Business Appliances
Watch our tutorial on how to enable HTTPS inspection on our 700 Appliance to improve your small business security. More information:
Cмотреть видео
Cмотреть видео
HD 00:03:55
Check Point: Deploy Small Business Appliances with the Zero Touch Cloud Service
Watch our overview of the Zero Touch Cloud Service to see how you can save valuable time in the initial deployment of our small business security appliances. For more information:
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: SMB 700 Appliance - チェック・ポイントのSMB向け700アプライアンス・シリーズ
オールインワンのUTMで中小規模環境にエンタープライズ・レベルのセキュリティを提供するチェック・ポイントの700アプライアンス・シリーズをご紹介します。
Cмотреть видео
Cмотреть видео
HD 00:02:43
Check Point: Introduces Next-Generation Threat Prevention Appliances | Advanced Threat Prevention
Introducing the next-generation of appliances designed to unleash the full power of advanced threat prevention security for businesses of all sizes. For more information visit: Gen V Cyber Security is here: Infinity is the first conso...
Cмотреть видео
Cмотреть видео
HD 00:03:41
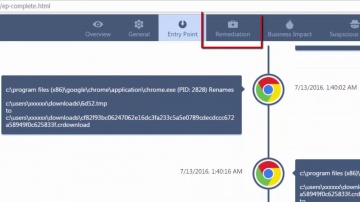
Check Point: Overview of SandBlast Agent Forensics Report | Tech Bytes
This video provides an overview of SandBlast Agent’s Forensics Report. SandBlast Agent defends endpoints and web browsers with a complete set of real-time advanced browser and endpoint protection technologies, including Threat Emulation, T...
Cмотреть видео
Cмотреть видео
HD 00:04:19
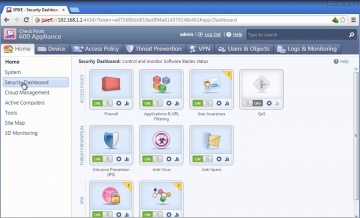
Check Point: SMB Cyber Security - 600 Appliance Setup
Small businesses need cost-effective security that provides robust protections and ease of use. For more information: brings its long-standing history of security expertise to a range of solutions optimized for the unique demands of smal...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: 600 Security Appliance: One Box, Complete Protection | SMB Cyber Security
Learn more about the 600 appliance: The 600 provides a complete security package with firewall, VPN, antivirus, intrusion prevention and more, at a price your small business can afford.
Cмотреть видео
Cмотреть видео
HD 00:06:47
Check Point: Unveils New Network Security Appliance Models
Gabi Reish, Head of Product Management at Software Technologies, introduces the new 2012 line of Appliances. For more information: provides organizations of all sizes with the latest data and network security protection in an integrated...
Cмотреть видео
Cмотреть видео
HD 00:05:12
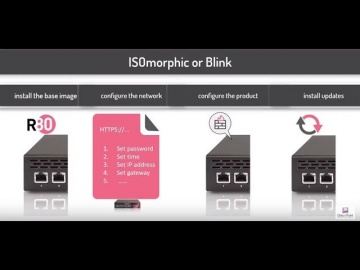
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:04:19
Check Point: 600 Appliance Setup
Watch our tutorial on how to setup our 600 Appliance, 's latest edition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: DDoS Protector - Technical Overview | DDoS Protection
's new Threat Emulation Software Blade prevents infections from undiscovered exploits, zero-day and targeted attacks. For more information: This innovative solution quickly inspects suspicious files, emulates how they run to discover mali...
Cмотреть видео
Cмотреть видео
HD 00:05:30
Check Point: Denial of Service Cyber Attack Protector Overview
DDoS Protector™Appliances block Denial of Service attacks within seconds with multi-layered protection and up to 40 Gbps of performance. For more information: Modern DDoS attacks use new techniques to exploit areas where traditional secu...
Cмотреть видео
Cмотреть видео
HD 00:05:08
Check Point: Advanced Cloud Security - CloudGuard Overview
For more information visit on advanced cloud security solutions visit, Discover CloudGuard, 's advanced cloud security solution. The cloud enables business benefits like agile computing and elastic scalability, but also introduces new clou...
Cмотреть видео
Cмотреть видео
HD 00:18:35
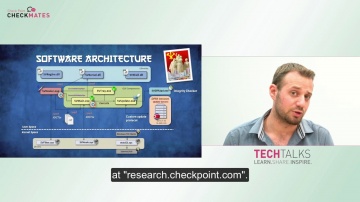
Check Point: CheckMates TechTalk: Analysis of SiliVaccine
SiliVaccine is an Anti-Virus tool used in North Korea. Security Researchers at got a copy of it to see if it had any abnormal behavior or undocumented features. Sure enough, it did!
Cмотреть видео
Cмотреть видео
HD 01:32:38
SCP Overview
На вебинаре мы расскажем о регистрации в SAP Cloud Platform и использовании сервисов платформы. Затем рассмотрим пример разработки приложения на базе предоставленного шаблона.
Cмотреть видео
Cмотреть видео
HD 00:10:57
Диасофт: Diasoft XBRL Engine (without subtitles)
IT-решение для некредитных финансовых организаций для перехода на отчетность в формате XBRL от Diasoft. В программе учтены все актуальные версии таксономии XBRL Банка России. Узнайте историю создания формата XBRL, о приходе юрисдикции XBRL ...
Cмотреть видео
Cмотреть видео
HD 00:27:53
Yandex.Cloud: Overview of the Yandex.Cloud platform - видео
Site: https://cloud.yandex.com/en-ru/ Console: https://console.cloud.yandex.com Documentation: https://cloud.yandex.com/en-ru/docs Introductory grant (up to $12 000 USD) and cost calculator: https://cloud.yandex.com/en-ru/prices
Cмотреть видео
Cмотреть видео
HD 00:22:53
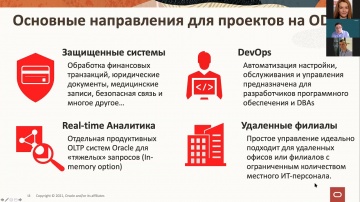
Oracle Exadata X8 Overview
Oracle EVP Juan Loaiza gives a quick overview of Exadata X8 capabilities for OLTP, analytics, cloud, and Autonomous Database.Анонсировано новое поколение систем Oracle Exadata, в основе которого существенное усовершенствование аппаратного и...
Cмотреть видео
Cмотреть видео
HD 01:29:58
СУБД Oracle: опыт использования Oracle Database Appliance для консолидации СУБД Oracle и приложений
Эксперты Oracle Иларион Моторин и Дмитрий Палецкий рассказали о возможностях консолидации баз данных и приложений на простом в управлении и удобном в развертывании программно-аппаратном комплексе Oracle Database Appliance, а представители о...
Cмотреть видео
Cмотреть видео
HD 00:30:03
Check Point: IoT & Industrial Cyber Attacks - Myth or Reality?
There is a lot of hype around how IoT will be able to change our lives, make us smarter, more efficient and more connected than ever. On the other end some site the potential danger this revolution will bring assuming IoT will not be arch...
Cмотреть видео
Cмотреть видео
HD 00:27:50
Check Point: vSEC on AWS Cloud Use Case and Best Practices
Moving computing resources and data to public clouds means security responsibilities become shared between you and your cloud provider. While infrastructure protection is delivered by the provider, customers are responsible for protecting ...
Cмотреть видео
Cмотреть видео
HD 00:31:47
Check Point: Latest Innovations in Cyber Defense
In this session, we are going to see and use the latest protections from SandBlast Network and SandBlast Agent against the recent strains of malware and security risks from 2017.
Cмотреть видео
Cмотреть видео
HD 00:26:26
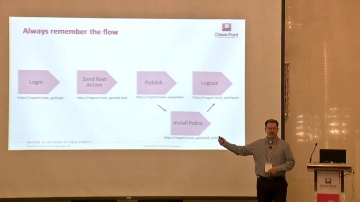
Check Point: Automating the Rulebase
From beginning to scripting, learn how to get started and automate common tasks in the rule base using R80.10 and common scripting/orchestration tools. Get the tools needed and learn some orchestration tips from 's automation experts
Cмотреть видео
Cмотреть видео
HD 00:06:01
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
HD 00:22:35
Check Point: Architecting Consolidated Security with Infinity
Presenting The Good, The Bad and The Ugly. Where does your company’s architecture fit? Learn how to build the best Infinity architecture and chime into a live interview listening to those who have transformed Ugly into Good.
Cмотреть видео
Cмотреть видео
HD 00:44:35
Check Point: Ask Us Anything: Dr. Dorit Dor and Team
Dr. Dorit Dor, Vice President of Products at , leads the company’s product management, business development, research and development (R&D) and quality assurance (QA). Together with the amazing product team at , they lead the initiatives fr...
Cмотреть видео
Cмотреть видео