Поиск по тегу «mobile security» в разделе Видеокаталог
HD 00:18:31
Check Point: Cyber Security in the Era of Exponential Technology
Amnon Bar-Lev - President, Software We are in an extraordinary time in human history. Thanks to innovative and disruptive technologies we live longer, healthier and more educated than ever before. While technologies such as cloud computin...
Cмотреть видео
Cмотреть видео
HD 00:16:07
Check Point: Moving to the Public Cloud, Securely - FireChat with AWS & Azure
More than 70% of the organizations are committed to a cloud strategy in 2017. Businesses are moving their applications to the Cloud to gain more agility and efficencies. At the same time, Cloud security remains their top concern. Customers...
Cмотреть видео
Cмотреть видео
HD 00:20:33
Check Point: We Make Jeans; How Hard Can That Be?
This talk will present some of the business challenges, experiences and road maps from a security perspective to protect the global Levi Brand. Steve Zalewski, Chief Security Architect, Levi Strauss For more information:
Cмотреть видео
Cмотреть видео
HD 00:04:32
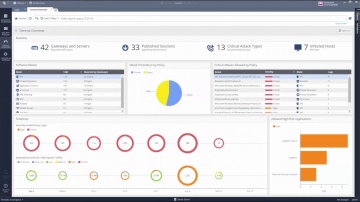
Check Point: R80.10 Security Management | Tech Bytes: Gateways, Logs, and Manage & Settings
This video is an overview that describes important features and functionality of the R80.10 SmartConsole. More information: To learn more about R80.10 Security Management: Infinity is the only fully consolidated cyber security architec...
Cмотреть видео
Cмотреть видео
HD 00:01:25
Check Point: Advanced Cyber Security for 2018 | Infinity
Learn more at Introducing Infinity, the world’s most advanced cyber security and management architecture. Infinity consolidates security across network, cloud and mobile, keeping you secured from known and unknown threats, today and in ...
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: Technical Assistance Center | Network Security Support
's team of vigilant security experts are here to help our customers. Well trained engineers are available to assist you 24/7 via web service request, live chat, or by phone. For more information:
Cмотреть видео
Cмотреть видео
HD 00:03:20
Check Point: 2017 Mobile Security Media Tour
Our Michael Shaulov, Head of Product, Mobile Security discusses the importance of mobile security and common vulnerabilities and threats mobile data of individuals and the enterprise. For more information:
Cмотреть видео
Cмотреть видео
HD 00:02:12
Check Point: Anatomy of a Smishing Attack: Czech Posta App
A new smishing attack targeted users in the Czech Republic was discovered January 26, 2017. Smishing, or SMS phishing, is a vector attackers use to send SMS messages from supposedly legitimate organizations. These messages persuade users t...
Cмотреть видео
Cмотреть видео
HD 00:02:37
Check Point: Protecting Mobile Devices Together - ElevenPaths – Telefonica and | Mobile Security
“Mobile devices are critical to the way we do business today. With cyberattacks growing in sophistication and frequency, exposing both the business and personal data we store on smartphones and tablets, mobile devices are the newest enterpr...
Cмотреть видео
Cмотреть видео
HD 00:01:50
Check Point: Hamas’ Cyber Tactics Exposed - Attacking IDF Soldier’s Mobile Phones
The Israeli Defense Forde uncovered a Hamas network that reached out to IDF soldiers online, sometimes in romantic ways, and ask them to download applications that would infect them with Trojan horse viruses. The applications used by Hamas ...
Cмотреть видео
Cмотреть видео
HD 00:03:03
Check Point: Koch Media Crushes Advanced Attacks with SandBlast | Advanced Threat Prevention
Koch Media develops games globally, which is a process fraught with peril to the intellectual property in their games. Koch sought to replace Cisco and decided on SandBlast Zero DayProtection to crush advanced attacks. For more informat...
Cмотреть видео
Cмотреть видео
HD 00:01:41
Check Point: From HummingBad to Worse: Android Malware Campaign | SandBlast Mobile Security
For five months, mobile threat researchers had unprecedented access to the inner-workings of Yingmob, the Chinese cyber criminals behind HummingBad, a malware that establishes a persistent rootkit on Android devices, generates fraudulent a...
Cмотреть видео
Cмотреть видео
HD 00:01:34
Check Point: DressCode Android Malware Discovered on Google Play | SandBlast Mobile Security | Andro
The mobile threat prevention research team discovered a new Android malware on Google Play, called DressCode, which was embedded into more than 40 apps, and found in more than 400 additional apps on third party app stores. notified Google...
Cмотреть видео
Cмотреть видео
HD 00:01:41
Check Point: Viking Horde: A New Type of Android Malware on Google Play | Mobile Security
Blog: More information: The research team uncovered a new Android malware campaign on Google Play it calls Viking Horde. Viking Horde conducts ad fraud, but can also be used for other attack purposes such as DDoS attacks, spam messages...
Cмотреть видео
Cмотреть видео
HD 00:01:15
Check Point: ââÑââÛâ»Ù¨â_Ä_ÄÝÎ_Ñ£ÐâäâÎÙâä
¾÷¬È_¨âµâ_ÄÄ__ø_»¨¾äÜ£ø_ª_ªá¤_ªÇ»â_Ûâ_Ä_Ä_ÄöÄ¥â©Ä_âãâÀÄÐÄÂÄÄÄöÜâ侩Ùø ¾ÄÉʱâÕã¬ââ¡Á÷ÇÝÑÀà¼Ñ_ªÛââµâ_ÄÄ__ø_»ÛÉøâ»Ä_ÄÂÄ_Ä â£Ä_â¡ÄÈâáâ_Ä ÄÊÛÄÄÄ...
Cмотреть видео
Cмотреть видео
HD 00:03:59
Check Point: Pokemon GO Repackaged Malware Demonstration | SandBlast Mobile Security Demo
The excitement over the new game Pokemon GO has taken the world by storm. Because it's available only in limited countries right now, some people may be tempted to download the app from sources other than Google Play or the Apple App Store....
Cмотреть видео
Cмотреть видео
HD 00:02:48
Check Point: Samsung Research America Chooses Mobile Threat Prevention
As the research arm of an industry-leading manufacturer of consumer electronics, Samsung Research America is committed to forward-looking innovation and bringing new products to market ahead of competitors. More Info: The last thing it n...
Cмотреть видео
Cмотреть видео
HD 00:04:02
Check Point: SideStepper: Anatomy of an iOS Vulnerability | Mobile Threat Prevention
For more information, visit: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: disclosed details about SideStepper, a vulnerability that can be used to install malicious enterprise apps o...
Cмотреть видео
Cмотреть видео
HD 00:01:32
Check Point: SandBlast Mobile Security: Man-in-the-Middle Mobile Attacks
Our mobile devices are more vulnerable then we think. A man-in-the middle attack is a potential threat every time you connect to a Wi-Fi network. For more information: Imagine you are at a coffee shop and you want to connect to Wi-Fi and...
Cмотреть видео
Cмотреть видео
HD 00:02:11
Check Point: Ä¢Äâ_ÄÇãɬø__Ð
More information: Report: IDC Technology Spotlight: Why Comprehensive Security Requires Mobile Threat Prevention: Protecting Your Enterprise From Mobile Threats (Japanese Subtitles) Keeping your business safe from cyberattacks is no ea...
Cмотреть видео
Cмотреть видео
HD 00:02:17
Check Point: Big Bad Mobile Threats of 2015 - Mobile Threat Prevention
The mobile threat landscape changed dramatically in 2015. Simple hacks and rudimentary malware was quickly replaced by sophisticated cyber thieves who know exactly what sensitive data they can take from you and how. Along with the growing s...
Cмотреть видео
Cмотреть видео
HD 00:01:10
Check Point: RSA 2016: Prevent Cyberattacks from Entering the Endpoint with SandBlast Agent
More information:
Cмотреть видео
Cмотреть видео
HD 00:01:18
Check Point: RSA 2016: Mobile Threat Prevention | Mobile Security
For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:01:46
Check Point: RSA 2016: Day 1 - Software
For more information visit: An overview of RSA 2016, Day 1 with Software.
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Hackers constantly modify their strategies and techniques to evade detection by traditional sandboxes to reach corporate resources. For more information visit: SandBlast Zero-Day Protection, with evasion-resistant malware detection, pro...
Cмотреть видео
Cмотреть видео
HD 00:03:39
Check Point: Mobile Threat Prevention Demo - Malware Invasion on an iOS Device
In this video, demonstrates an end-to-end threat and remediation situation on an iOS device using Mobile Threat Prevention. To learn more about Mobile Threat Prevention for iOS and Android devices, visit Report: IDC Technology Spotligh...
Cмотреть видео
Cмотреть видео
HD 00:01:12
Check Point: : A Founding Member of the AirWatch Mobile Security Alliance | Mobile Threat Prevention
President Amnon Bar-Lev addresses the audience during the keynote speech at AirWatch Connect 2015 in Atlanta on September 22, 2015, and announces ’s participation as a founding member of the AirWatch Mobile Security Alliance.
Cмотреть видео
Cмотреть видео
HD 00:02:45
Check Point: SandBlast Zero-Day Protection | Advanced Threat Prevention
Learn how to take the first steps to enable your security gateway to leverage the SandBlast Cloud Service or the SandBlast Appliance. Learn more at: See what end users would experience, and what security administrators can expect to see. ...
Cмотреть видео
Cмотреть видео
01:03:03
Check Point: Stay One Step Ahead with SandBlast Zero-Day Protection
Watch this webcast to learn about SandBlast Zero-Day Protection, an innovative approach to stop unknown malware, zero-day and targeted attacks from infiltrating networks. More information: Zero-day protection offering network security wi...
Cмотреть видео
Cмотреть видео
HD 00:01:45
Check Point: Preventing Tomorrow's Cyber Security Threats
Increasing your enterprise security often means increasing your complexity and management challenges in kind. For more information, visit Growing complexity in security infrastructure puts a huge strain on the efficiency of the security o...
Cмотреть видео
Cмотреть видео