Поиск по тегу «infinity» в разделе Видеокаталог
HD 00:18:09
Разработка iot: Эра Интернета вещей. Зачем нужен Check Point NGFW для IoT? - видео
О безопасности IOT рассказывает Дмитрий Кудра, консультант по информационной безопасности Check Point
Cмотреть видео
Cмотреть видео
HD 01:12:00
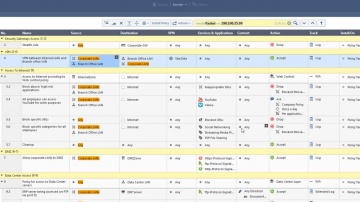
Что нового в R81 Management?
Никита Турков рассказывает об изменениях и новом функционале в управлении R81 - единой платформе кибезбезопасности.Вопросы, обсуждаемые в этом вебинаре: - Профили Infinity Treat Prevention - Объекты Data Center Query - Новая NAT полит...
Cмотреть видео
Cмотреть видео
HD 00:25:18
Check Point и DevSecOps: безопасность в новой эре разработки ПО
Микросервисы, контейнеры, Kubernetes, DevOps, DevSecOps – эти термины все прочнее входят в нашу жизнь. Даже самые консервативные организации начинают использовать такие технологии. А многие уже в полной мере вкусили их преимущества. Но к...
Cмотреть видео
Cмотреть видео
HD 00:29:35
CloudGuard IaaS: динамическая сетевая безопасность в отечественных и зарубежных облаках - ви
Амир Алиев, консультант по информационной безопасности, Check Point Software Technologies Задействовав ресурсы публичного облака у вас может возникнуть вопрос - где здесь безопасность и кто за нее отвечает? а докладе вы узнаете ответ на эт...
Cмотреть видео
Cмотреть видео
HD 00:27:13
iot: Безопасная экосистема Интернета вещей (IoT) - видео
Do you trust your IoT devices? Itzik Feiglevitch, Product Manager, Check Point Software TechnologiesРастущие с экспоненциальной скоростью устройства Интернета вещей приносят значительную ценность бизнесу, развивая и расширяя его возможности...
Cмотреть видео
Cмотреть видео
HD 00:05:12
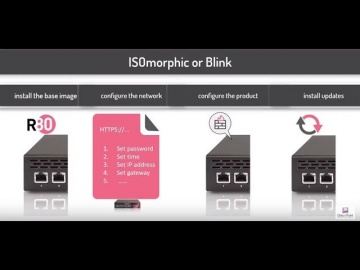
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:50:38
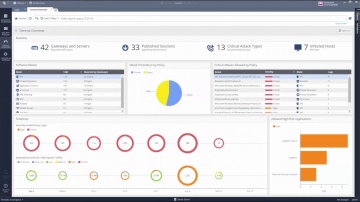
Check Point: Advanced Cyber Security for 2018 | Introducing 3 New products: Step into Gen-V of Cyber
For more information: is happy to welcome the 5th Generation of Cyber Security with 3 exciting new offerings: Infinity Total Protection (ITP), CloudGuard, and Smart-1 Security Management Appliances. • Infinity Total Protection is a gam...
Cмотреть видео
Cмотреть видео
HD 00:02:49
Check Point: Advanced Cyber Security for 2018 | Prevent Gen V Cyber Attacks with Infinity
More information: ... Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the fut...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
HD 00:17:04
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
HD 00:06:01
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
HD 00:03:33
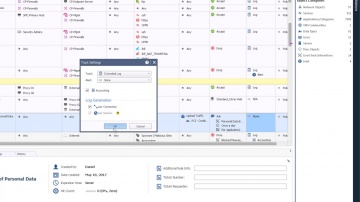
Check Point: Continuing Policy Work-in-Progress with R80.10 Session Take Over | Tech Bytes
R80.10 enables security administrators to work on the same policy at the same time. But what happens if a project needs to be finished and the security administrator is not available to do so? R80.10 Session Take Over feature allows for oth...
Cмотреть видео
Cмотреть видео
HD 00:03:13
Check Point: Managing Security Policy Changes with R80.10 | Tech Bytes
When new services are introduced and your security policy needs to be adjusted accordingly, what tools will you be using? R80.10 makes it easier to implement changes. The “Where Used” and “Replace” tools will help security administrators ma...
Cмотреть видео
Cмотреть видео
HD 00:04:30
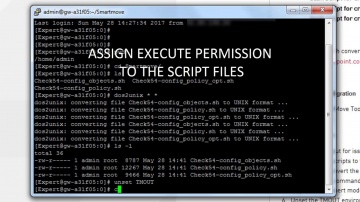
Check Point: Converting Another Vendor's Security Policy to is a SmartMove | Tech Bytes
offers migration tools and assistance to migrate your security policy from another vendor to . This video shows how you can use the SmartMove tool to migrate from Cisco to . To learn more about SmartMove in CheckMate visit:
Cмотреть видео
Cмотреть видео
HD 00:04:03
Check Point: Use R80.10 New Packet Mode Feature to Search Through Policy
Packet Mode, a new feature introduced within R80.10, enables you to search the rule base as if it were a packet going through the security policy. For more information visit: R80.10 features the most advanced threat prevention across netw...
Cмотреть видео
Cмотреть видео
HD 00:24:49
Check Point: Welcome to the Future of Cyber Security | Infinity
The future of cyber security is here. Learn and stay protected against today's cyber threat landscape. For more information: We are all living in a connected world which is affecting every aspect of our lives. In the past couple of ye...
Cмотреть видео
Cмотреть видео
HD 00:26:30
Check Point: Infinity | The Cyber Security Architecture of the Future
Gabi Reish - VP, Product Management and Product Marketing, Software For more information on the Cyber Security Architecture of the Future, please go to:
Cмотреть видео
Cмотреть видео
HD 00:04:47
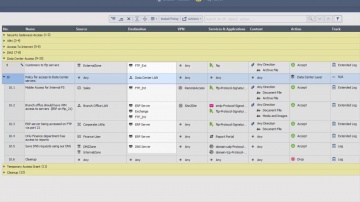
Check Point: R80.10 SmartConsole Security Policies View | Threat Prevention
This video is an overview that describes important features and functionality of the R80.10 SmartConsole and focuses on: Unified Access and Threat Prevention Policies Example of inline layers for zone-based policy Using multiple blades in o...
Cмотреть видео
Cмотреть видео
HD 00:05:27
Check Point: Start Building Your Unified Policy with R80.10 | Security Management | Tech Bytes
R80.10 policy management is unified so you can create and monitor these policies harmoniously. One single policy manages your users, devices, applications, data and networks. With this unified policy, you also get unparalleled granular cont...
Cмотреть видео
Cмотреть видео
HD 00:04:32
Check Point: R80.10 Security Management | Tech Bytes: Gateways, Logs, and Manage & Settings
This video is an overview that describes important features and functionality of the R80.10 SmartConsole. More information: To learn more about R80.10 Security Management: Infinity is the only fully consolidated cyber security architec...
Cмотреть видео
Cмотреть видео
HD 01:03:18
Check Point: and Tufin: Security Management for the Future | Enterprise Network Security
and Tufin provide complete, simplified and automated security management for the enterprise network of the future. For more information: Together, the Tufin Orchestration Suite with Firewalls and Security Management products provide ad...
Cмотреть видео
Cмотреть видео
HD 00:07:14
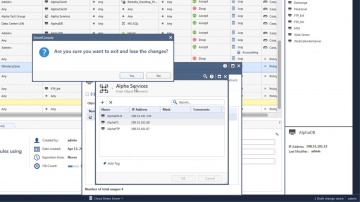
Check Point: Creating Host Objects with R80 Management API Tutorial | Security Management Tutorial
How to use R80 Management API to run a BASH script that automatically creates host objects in the Security Management server database. For more information: This video tutorial is intended for users that are familiar with automation scri...
Cмотреть видео
Cмотреть видео
HD 00:02:11
Check Point: R80 Streamlines Security Management at Appvion | Data Center Security
Appvion, a manufacturer of specialty papers, tested R80 security management during development and now uses it every day to gain efficiency, high visibility and concurrent management capabilities.
Cмотреть видео
Cмотреть видео
HD 00:04:01
Check Point: Tutorial: Configuring Application Control
How to use R80 SmartConsole to get started with the Application Control, URL Filtering Software Blades, and URL Filtering Settings with R80 Security Management. For more information: Infinity, the first consolidated security across net...
Cмотреть видео
Cмотреть видео
HD 00:03:30
Check Point: Tutorial: Configuring IPS Settings with R80 Security Management Server | Advanced Threa
How to use R80 SmartConsole to configure the settings for the IPS Software Blade. For more information visit:
Cмотреть видео
Cмотреть видео
HD 00:00:39
Check Point: Automation with VMware vCenter Orchestrator and R80 Smart Management
Use VMware vCenter Orchestrator to provision security policies in Ûªs R80 Smart Management Console leveraging the open API interface. This video demos automated security policy provisioning. Rules that are provisioned include Stealth rul...
Cмотреть видео
Cмотреть видео
HD 00:01:48
Check Point: vSEC controller Demo with R80 Smart Management | Cloud Security
This video demos the vSEC cloud security integration with VMware vCenter and NSX. It shows you how to integrate a vCenter server in the Smart Console, provision a security rule based on imported vCenter objects like VM name, integrate wit...
Cмотреть видео
Cмотреть видео
HD 00:01:25
Check Point: R80 Security Management | Advanced Threat Prevention
's R80 Security Management helps you consolidate security functions so you can be more efficient and effective at deploying the strongest protections across your organization. More Information:
Cмотреть видео
Cмотреть видео
HD 00:01:28
Check Point: RSA 2016: R80 Security Management Launch | Security Management Software
For more information: Organizations that possess consolidated security simplify complex environments, improve efficiency and ensure security is consistently deployed across the organization. Change the way you manage security with integra...
Cмотреть видео
Cмотреть видео
HD 00:01:44
Check Point: Security Management Customer Success Story: Talisys | R80 Security Management
More information on R80 Security Management visit Talisys, an innovator in financial securities processing software, leverages R80 to reduce security management complexity. Building on Ûªs leadership in speedy root cause analysis, they a...
Cмотреть видео
Cмотреть видео