Check Point: Unveils New Network Security Appliance Models → Похожие видео ролики
Gabi Reish, Head of Product Management at Software Technologies, introduces the new 2012 line of Appliances. For more information: provides organizations of all sizes with the latest data and network security protection in an integrated next generation firewall platform, reducing complexity and lowering the total cost of ownership. Whether you need next-generation security for your data center, enterprise, small business or home office, has a solution for you.
Подробнее в видео...
Подробнее в видео...
HD 00:04:41
Check Point: 700 Appliance Setup | SMB Cyber Security
For more information: Watch our tutorial on how to setup our 700 Appliance, 's latest addition to the product family to protect small businesses against the latest cyber threats.
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: 700 Series Appliances for Small Business - Product Video | SMB Cyber Security
As a small business, your focus is on building unique products, driving sales, and providing excellent service to your customers. Security is important but it seems like every week there is some new piece of software or equipment to prote...
Cмотреть видео
Cмотреть видео
HD 00:01:55
Check Point: Optimizes Security with Gigamon’s Full Network Visibility
and Gigamon’s joint solution provides comprehensive network visibility, optimal performance and advanced threat prevention capabilities. For more information:
Cмотреть видео
Cмотреть видео
HD 01:03:18
Check Point: and Tufin: Security Management for the Future | Enterprise Network Security
and Tufin provide complete, simplified and automated security management for the enterprise network of the future. For more information: Together, the Tufin Orchestration Suite with Firewalls and Security Management products provide ad...
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: Technical Assistance Center | Network Security Support
's team of vigilant security experts are here to help our customers. Well trained engineers are available to assist you 24/7 via web service request, live chat, or by phone. For more information:
Cмотреть видео
Cмотреть видео
00:43:43
Check Point: Q&A: Compliance and Regulations with Jeremy Kaye | Network Security Risk and Compliance
For more information: On June 18, 2013, 's in house #regulations and #compliance expert Jeremy Kaye spoke with Dameon Welch-Abernathy live in our first Google+ Hangouts on Air. This was an opportunity to hear some of the challenges your p...
Cмотреть видео
Cмотреть видео
HD 00:03:58
Check Point: Compliance Software Blade | Network Security Best Practices
For more information: This is the second video in the Compliance Software Blade Demonstration Series. This video provides insight into aligning both security and compliance to security best practices.
Cмотреть видео
Cмотреть видео
HD 00:23:46
Check Point: Choosing The Right Security Architecture | Cyber Security | Network Security
Moti Sagey - Head of Strategic Marketing & Intelligence, Software When it comes to choosing the right security architecture & security vendor, what does it take to win your trust? In this session Moti Sagey will cover three key pillars th...
Cмотреть видео
Cмотреть видео
HD 00:02:00
Check Point: Anti-Bot Protection | IoT| Network Security
A bot is malicious software that allows cyber criminals to remotely control computers and execute illegal activities such as stealing data, spreading spam and distributing malware. More information: Anti-Bot security software detects bot...
Cмотреть видео
Cмотреть видео
HD 00:04:19
Check Point: SMB Cyber Security - 600 Appliance Setup
Small businesses need cost-effective security that provides robust protections and ease of use. For more information: brings its long-standing history of security expertise to a range of solutions optimized for the unique demands of smal...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: 600 Security Appliance: One Box, Complete Protection | SMB Cyber Security
Learn more about the 600 appliance: The 600 provides a complete security package with firewall, VPN, antivirus, intrusion prevention and more, at a price your small business can afford.
Cмотреть видео
Cмотреть видео
HD 00:01:58
Check Point: Hunze en Aa Water Resource Board enhances Network Security, SCADA Systems with SandBlas
For more information: To help ensure safe operation of its pumping stations and other key systems, the Hunze en Aa Water Resource Board implemented NGTX appliances with SandBlast zero-day protection. Through the solutions centralized mana...
Cмотреть видео
Cмотреть видео
HD 00:03:43
Check Point: The Threat of Bots and Botnets | IoT | Network Security
Learn More: explains: What is a bot? What is a botnet? What is an Advance Persistent Threat?
Cмотреть видео
Cмотреть видео
HD 00:03:18
Check Point: Advanced Network Security: New Anti-Bot Software Blade
Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention. More information: provides organizations of all sizes with the latest data and network security protection i...
Cмотреть видео
Cмотреть видео
00:05:19
Check Point: CRN Interviews Amnon Bar-Lev | Network Security
Amnon Bar-Lev talks to CRN about how to better target products for sales and that there should be a focus on evaluating existing network security architecture and protecting organizations.
Cмотреть видео
Cмотреть видео
HD 00:07:06
Check Point: 's SSL Inspection Technology | Enterprise Network Security
This video shares 's SSL Inspection technology against internal and external threats: This video provides a close look at 's SSL Inspection technology, which allows 's advanced security functions -- including Application Control, URL Fil...
Cмотреть видео
Cмотреть видео
HD 00:05:29
Check Point: Next Generation Firewall, How To Choose The Right One | Network Security
What questions should you ask when choosing the right network security protection in an integrated next generation firewall platform? For more information: provides customers of all sizes with the latest data and network security protect...
Cмотреть видео
Cмотреть видео
HD 00:02:38
Check Point: Your Second Pair of Eyes - Compliance Software Blade | Network Security
For more information: Keeping a close eye on security and compliance is a challenging task. The Compliance Software Blade can be your second pair of eyes to constantly monitor your security status, save time in preparing audits and compl...
Cмотреть видео
Cмотреть видео
HD 00:03:31
Check Point: Protecting Against Spy Eye Bot | Network Security
For more information: Learn how to protect against Spy Eye bot
Cмотреть видео
Cмотреть видео
HD 00:05:12
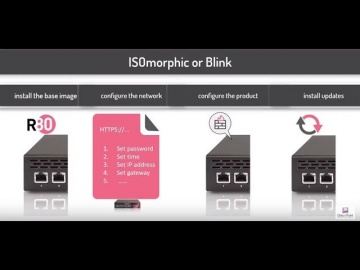
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:02:08
Check Point: Capsule Docs – Keep Your Business Documents Protected | Enterprise | Network Security
Capsule Docs protects your sensitive business documents to ensure they don’t get unintentionally exposed. See how Capsule Docs works to provide document security.
Cмотреть видео
Cмотреть видео
HD 00:01:24
Check Point: Capsule Docs - Secure Business Documents Everywhere | Network Security
Capsule Docs ensures that only authorized individuals can access your business documents. Confidently share documents with coworkers, business partners, clients, and vendors, because you are in control of their access and sharing rights.
Cмотреть видео
Cмотреть видео
HD 00:07:01
Check Point: Overview of the 61000 Appliance | Data Center Security Systems
For more information:
Cмотреть видео
Cмотреть видео
HD 00:04:08
Check Point: ThreatCloud | Complete Cyber Security Intelligence Infrastructure | Network Security
For more information: Introducing ThreatCloud, the first collaborative network to fight cyber-attacks.
Cмотреть видео
Cмотреть видео
HD 00:04:43
Check Point: Next-Generation Secure Web Gateway | Network Security
Learn More: Are you trying to secure Web 2.0 with 1.0 tools? The Web has evolved, threats have evolved, so should your Web Security! In this video, learn how to best protect against today's web-borne malware and help businesses to get th...
Cмотреть видео
Cмотреть видео
00:03:42
Check Point: Customer Success: The University of Liege Uses To Boost Network Security
The University of Liege in Belgium selects to help mitigate security issues around areas like BYOD and the increasing need for bandwidth. With 's 12600s and 12200s appliances in the data center and 2200s for its branch locations, the Univ...
Cмотреть видео
Cмотреть видео
HD 00:01:17
Check Point: Partner Insights -- Jason Lawrence, Sr. Network Security Advisor, Dataway
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Jason Lawrence of Dataway shares insights about 's model of annualized service behind its software blade architecture as well as 's cen...
Cмотреть видео
Cмотреть видео
HD 00:01:06
Check Point: RSA Conference 2014 - Customer Insights - Joseph Royal, Network Security Manager, Leido
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Joseph Royal of Leidos shares what makes him a fan.
Cмотреть видео
Cмотреть видео
HD 00:06:01
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
HD 00:22:35
Check Point: Architecting Consolidated Security with Infinity
Presenting The Good, The Bad and The Ugly. Where does your company’s architecture fit? Learn how to build the best Infinity architecture and chime into a live interview listening to those who have transformed Ugly into Good.
Cмотреть видео
Cмотреть видео